British e-Ticketing Service Breach Resulted in 4.8 Million Records Now for Sale
- A new threat actor is selling 4.8 million email addresses and passwords on the dark web.
- The database includes various email addresses belonging to UK government domains.
- The breach on the e-ticketing platform most probably happened through an “SQL Injection” attack.
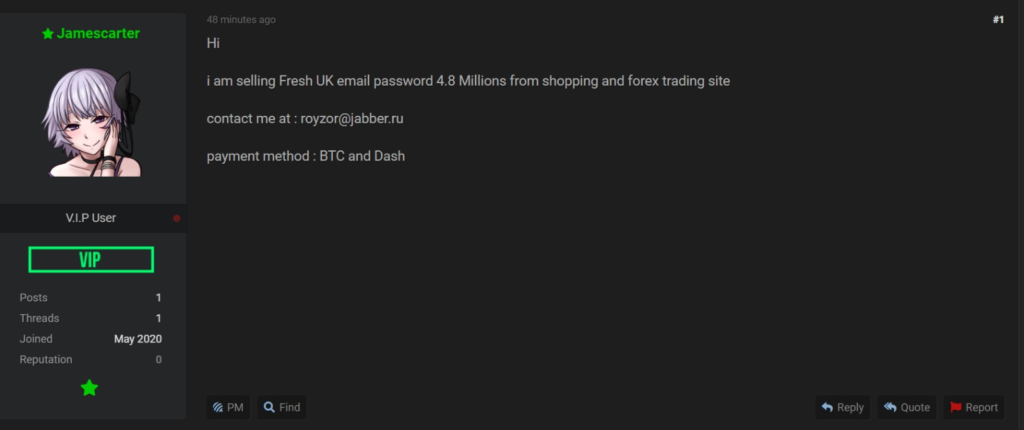
Using the “Jamescarter” nick, a threat actor has put up a massive database for sale on the dark web, which looks like it comes from a breach on a UK-based e-ticketing service. The discovery of the posting was the work of intelligence analysts at KELA, who tipped us about it.
KELA managed to acquire a sample of this data (10,000 records) for further analysis and figured that about 3% of the entries were duplicates. It means that the remainder 97% are unique combinations of email addresses and passwords.
The posting date is July 8, 2020, and the particular threat actor seems to be a new user who hasn’t sold anything else recently. The account on the market where the sale takes place was created in May 2020. KELA didn’t find any correlation with other active data brokers, so it seems that “Jamescarter” is a new entity that hasn’t established a reputation that would form the basis for collaborations with other groups.
The 4.8 million records are sold for $2,500, and there are several critical email addresses included. KELA has found emails from UK government domains such as the treasury.wa.gov.au, calderdale.gov.uk, surreycc.gov.uk, and redbridge.gov.uk by merely analyzing the data sample.
It means that there may be a lot more to be found in the entire database. Having administration email addresses in the data set indicates that the actors could access government agents' accounts and potentially even attack public platforms.
Regarding the freshness of the records, there are mixed indicators on that part. The actor maintains that the data is fresh since he/she obviously wants to sell it, but some entries are old beyond any doubt. For example, the researchers found an email address belonging to a Tesco domain that was discontinued two years ago. The data is likely a mix of old and fresh entries to inflate the volume and make the listing more alluring.
As for the e-ticketing platform, KELA didn’t manage to establish a communication with them yet, so we can’t name it for safety and security reasons. However, they did find them in a Pastebin list titled “websites vulnerable to SQL Injection,” so there may be a connection there although it's not absolutely certain. In fact, the same website was defaced by another hacker in the recent past, so the vulnerability was there.
READ MORE:
- Hackers Are Selling 62,000 Active eToro Accounts on a Dark Web Forum
- More Than 15 Billion Stolen Credentials Are Circulating Out There
- A Dark Web Data Broker Is Selling User Records Coming From 14 Companies