11 Best Encryption Software Tools for Every Job
There’s hardly a single aspect of using computer technology these days that hasn’t been touched by encryption technology. From inside our devices to out on the web. At some point, something is getting encrypted to protect the information in storage or transit.
For every possible use case of encryption, there’s a tool competing for your time offering to protect your information. With growing concerns related to personal privacy, corporate prying and government spying, it can be hard to figure out which encryption software tools are worth looking into. What you’ll find here are some of the best software encryption tools you can get today. Most of them have different specific uses, but they are all tools that you can use to apply the power of encryption to your own data.
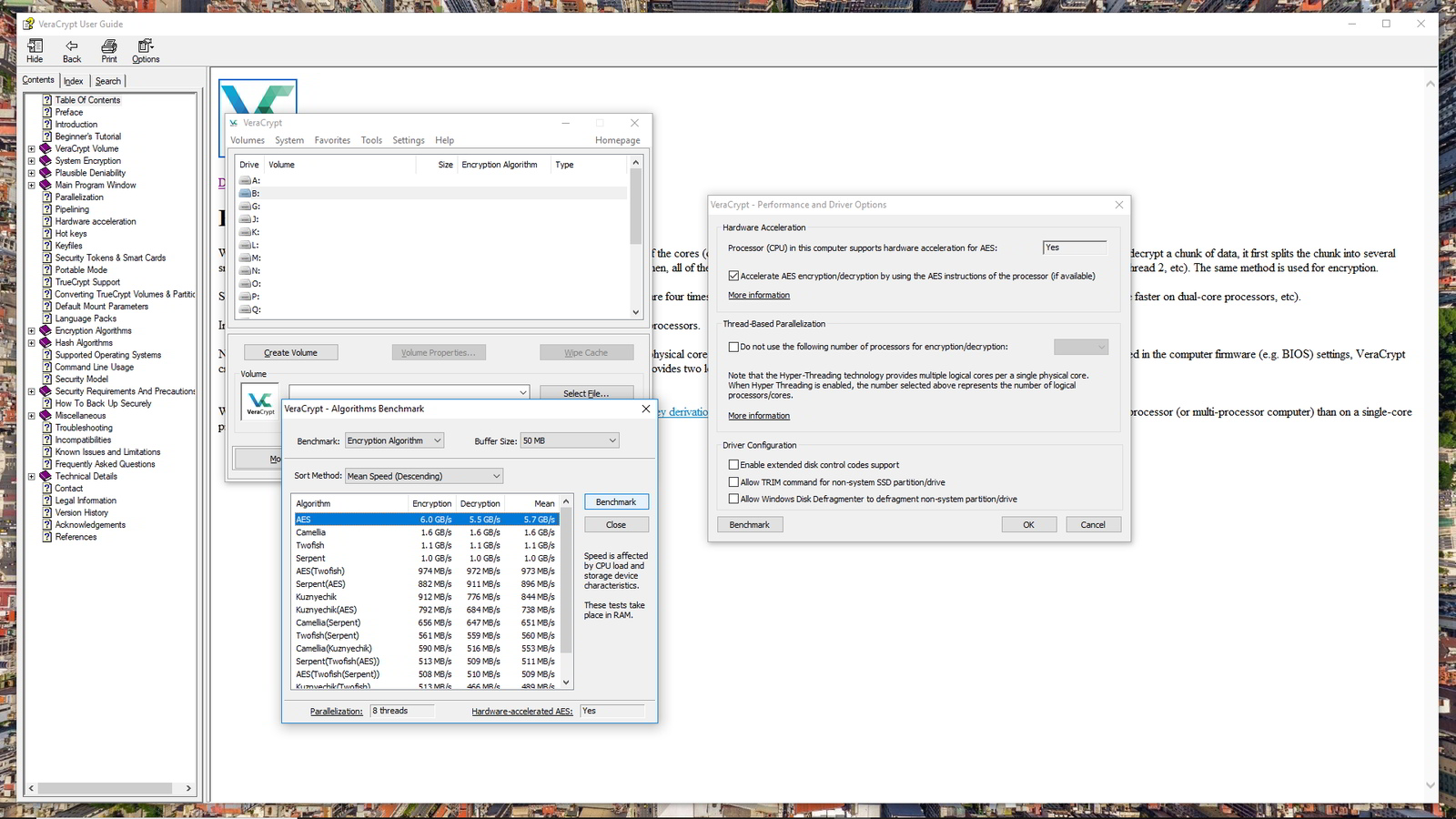
Veracrypt
Years ago, the darling of the disk encryption community was a little program known as TrueCrypt. You could use it to encrypt data on the fly and powerfully secure your data. In 2014 however, it was announced that TrueCrypt was no more. No further development would take place. Its source code was made available and the developers moved on.
Today the spiritual successor to TrueCrypt is VeraCrypt. It’s an Open Source fork of TrueCrypt and you can use it to encrypt your entire hard drive or just containers on an otherwise unencrypted disk.
Because it’s Open Source, there can be no backdoors. It actually fixes some of the few security holes that TrueCrypt had. It’s also moderately user-friendly in my opinion. It’s not what I would call a “casual” software package, but most average PC users would figure it out with a bit of light Googling at most.
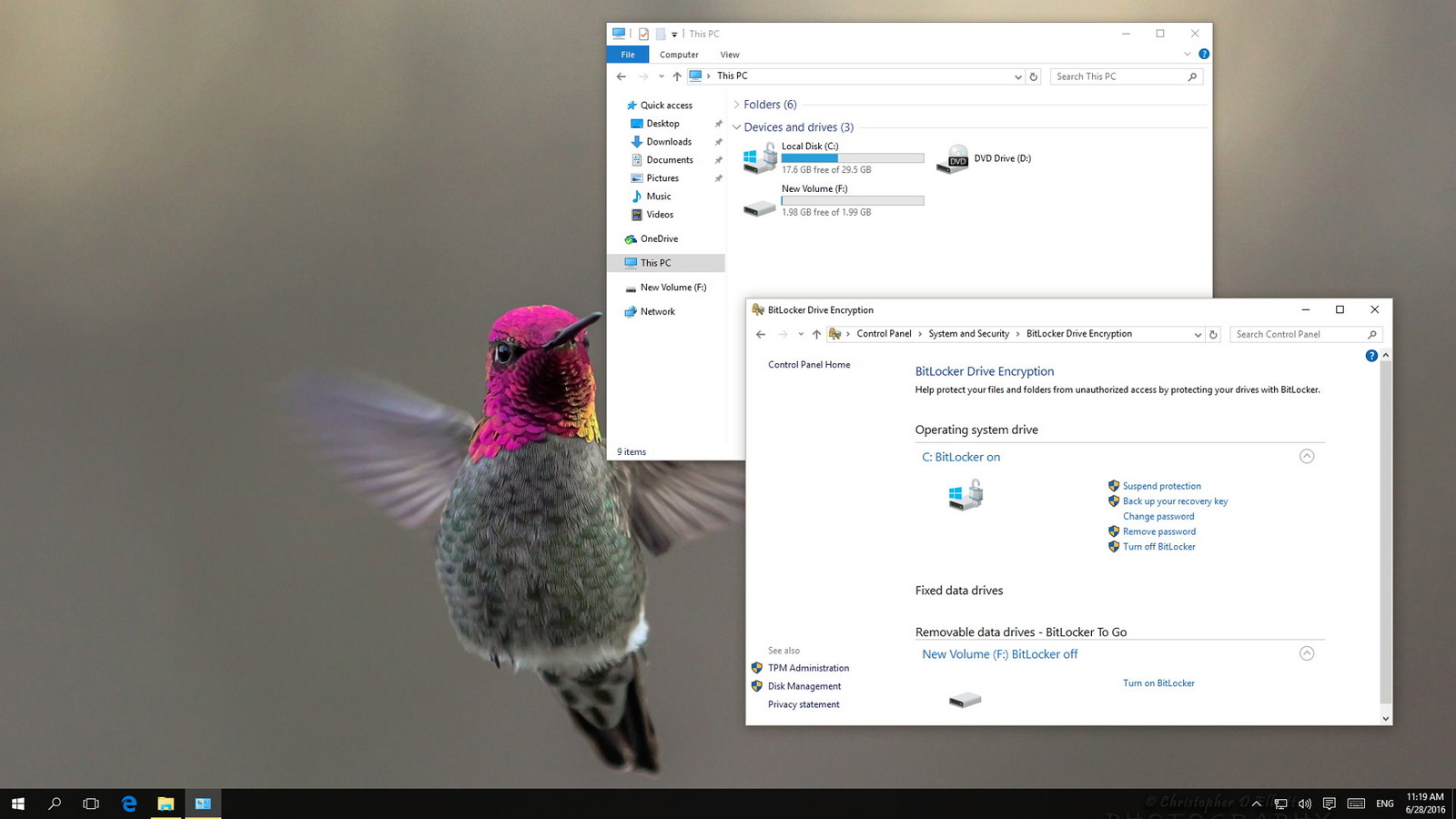
BitLocker
BitLocker and VeraCrypt are two software packages that do essentially the same job. The big difference is that BitLocker is a closed-source package that only comes with the fancier versions of Windows, such as Pro and Enterprise. It’s been around since Windows Vista.
In addition to only shipping with certain versions of Windows, BitLocker also requires a computer that has a TPM module. This is a hardware device that plays an important part in the encryption process. Without it, BitLocker won’t work for full disk encryption.
While it’s designed to provide seamless and invisible disk encryption, you can also use BitLocker to Go for removable media like flash drives.
BitLocker is a streamlined program without any extra fat. The best feature is how integrated and invisible it is. Once you have full-disk encryption enabled, you’ll quickly forget it's even there. If you already have a copy of Windows that comes with BitLocker, it’s a great choice to protect your computer. However, if you lack a TPM or don’t have the right version of Windows, VeraCrypt is the free alternative I would look to.
FileVault 2
Just as Windows has a built-in encryption tool, so does MacOS. It’s called FileVault and the latest version is FileVault 2. It’s a full disk encryption software package that makes sure no one without your account credentials can get to your files.
FileVault 2 is distinct from FileVault 1 in that the older program it could only encrypt the MacOS Home folder. Any Mac user with OS X 10.7 or higher can use this latest version of the software.
As a native Apple solution, FileVault 2 offers the most seamless experience for disk encryption on a Mac. However, there are some aspects of FileVault 2 which are less than optimal. It can have a significant effect on disk performance and processor load on older Mac hardware. Just because your old Mac can run the newer OS X versions, doesn’t mean your hardware will be up to it. Nonetheless, if you want that Apple user-friendliness and native reliability, FileVault should be your first stop.
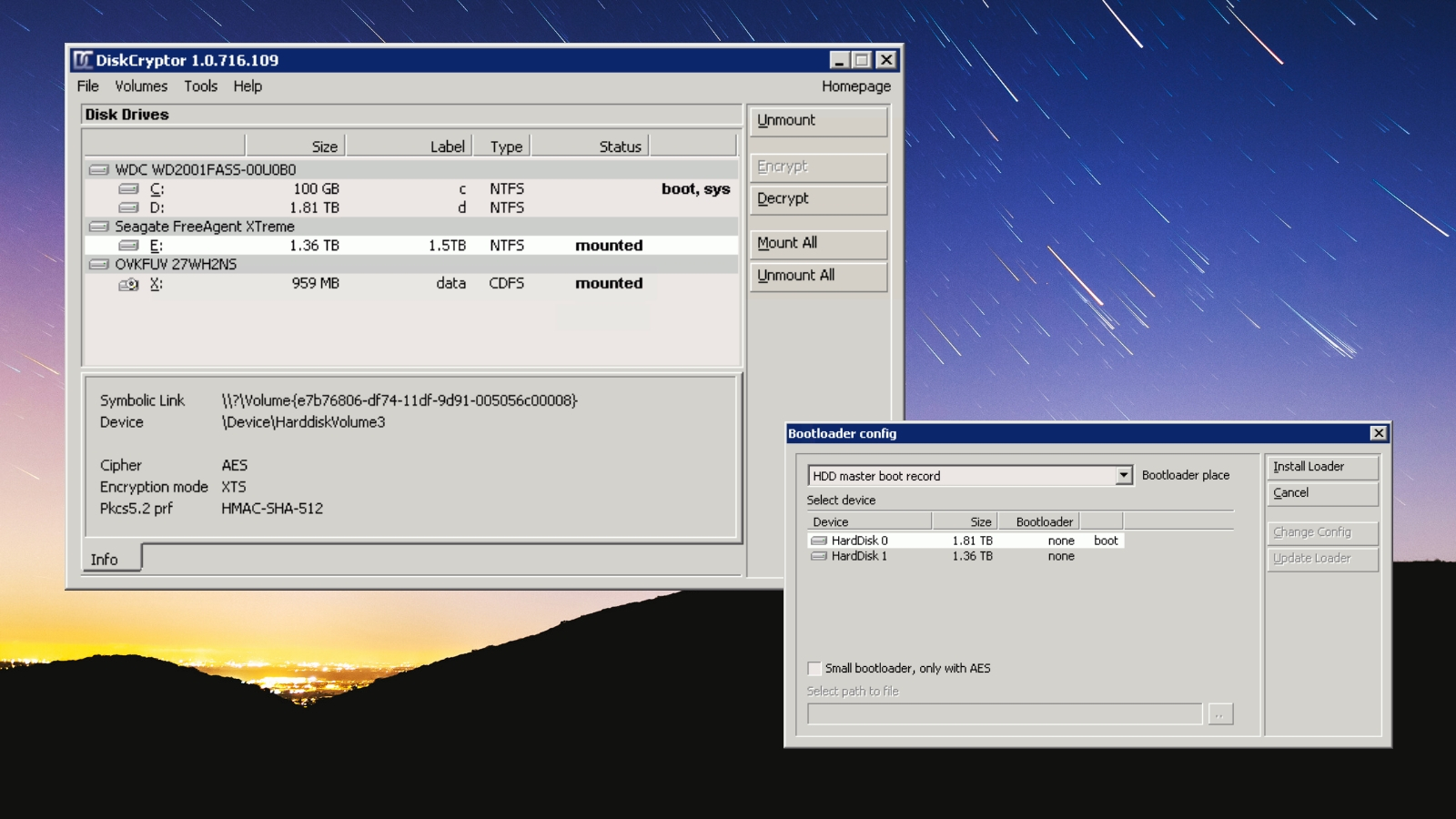
DiskCryptor
DiskCryptor joins the ranks of TrueCrypt and Veracrypt as an open source full-disk encryption program. It’s meant to be a free alternative to paid disk encryption packages. However, the major OSes now come with similar functionality built in, which means that’s not a major selling point anymore. That being said, open source alternatives should always be encouraged. They are also naturally resistant to back doors, which can be placed in closed source software by the developer at the behest of governments or other powerful actors.
DiskCryptor gives the user lots of control and allows for a selection of encryption standards. These include AES-256 and Twofish, which are both considered very powerful. DiskCryptor is pretty fast and the developers say it’s overhead is so light, you can barely tell it is there at all. This is largely due to good support for hardware acceleration through CPU and SSD features.
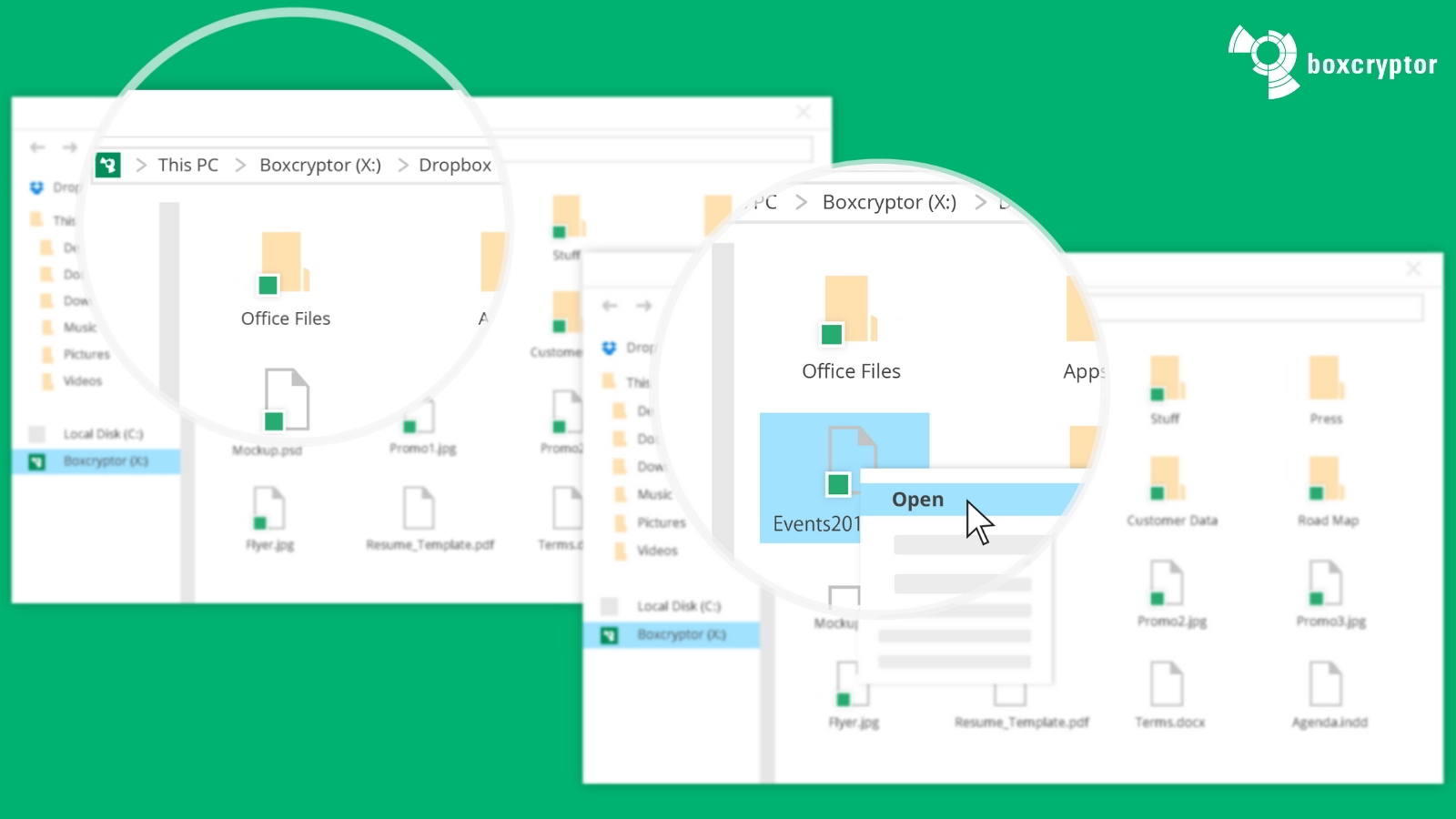
BoxCryptor
BoxCryptor is a program that lets you enjoy major commercial cloud storage services like DropBox, without giving the company access to your files. You see, although your cloud storage is encrypted, the provider has the keys. So they can take a peek whenever they want to. BoxCryptor uses end-to-end encryption to prevent this from happening. Not even BoxCryptor has access to your encryption keys.
It automatically detects all of the major cloud accounts on your computer and seamlessly integrates into the background. It’s the premier provider of zero-knowledge, end-to-end cloud storage encryption. It’s also awesome since you don’t have to drop whoever you are currently using. As long as your existing provider is on the list of 30 supported cloud storage services. The basic free tier gets you one provider and two devices, which will cover most users perfectly. This is a must-have service for those serious about their cloud privacy.
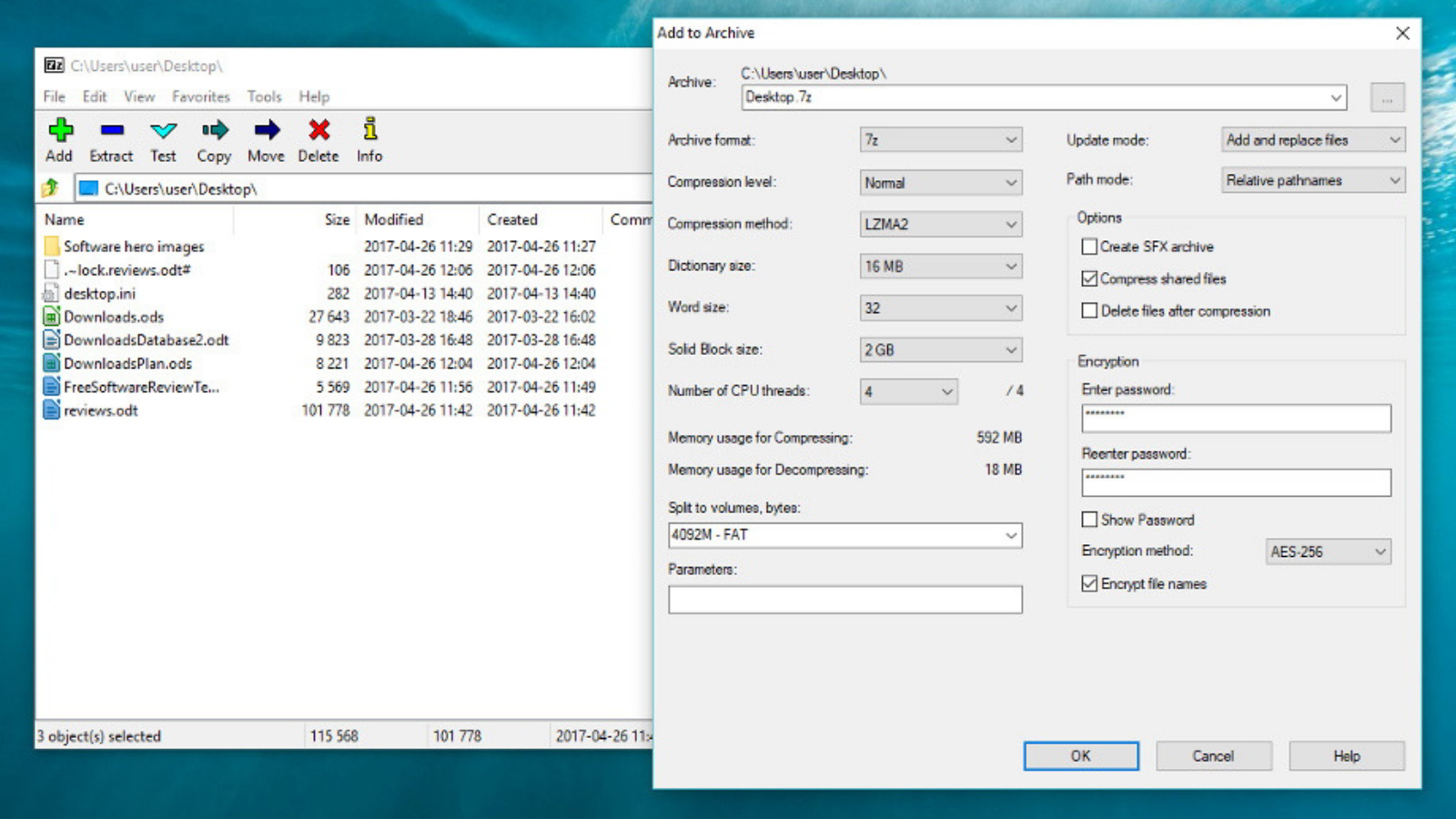
7-Zip
7-Zip has been my favorite compression program since before Windows had native support for files. It’s completely free, unlike WinZip, which you need to buy as soon as the trial period runs out.
The program integrates well with Windows and allows you to quickly compress and decompress folders. You can access it directly from the right-click menu in Windows Explorer. The reason it’s on this list is thanks to its encryption option. You can encrypt your zipped folders and then move them to whichever storage medium you like. 7-Zip is a wonderfully simple program. Although it could use a facelift. If you want a fast, powerful way to protect copies of some files, this is a great choice. Don’t think the encryption is lightweight though. 7-Zip uses AES-256. That’s more than most will ever need. Just about any Windows version made is compatible and Linux versions of the software also exist.
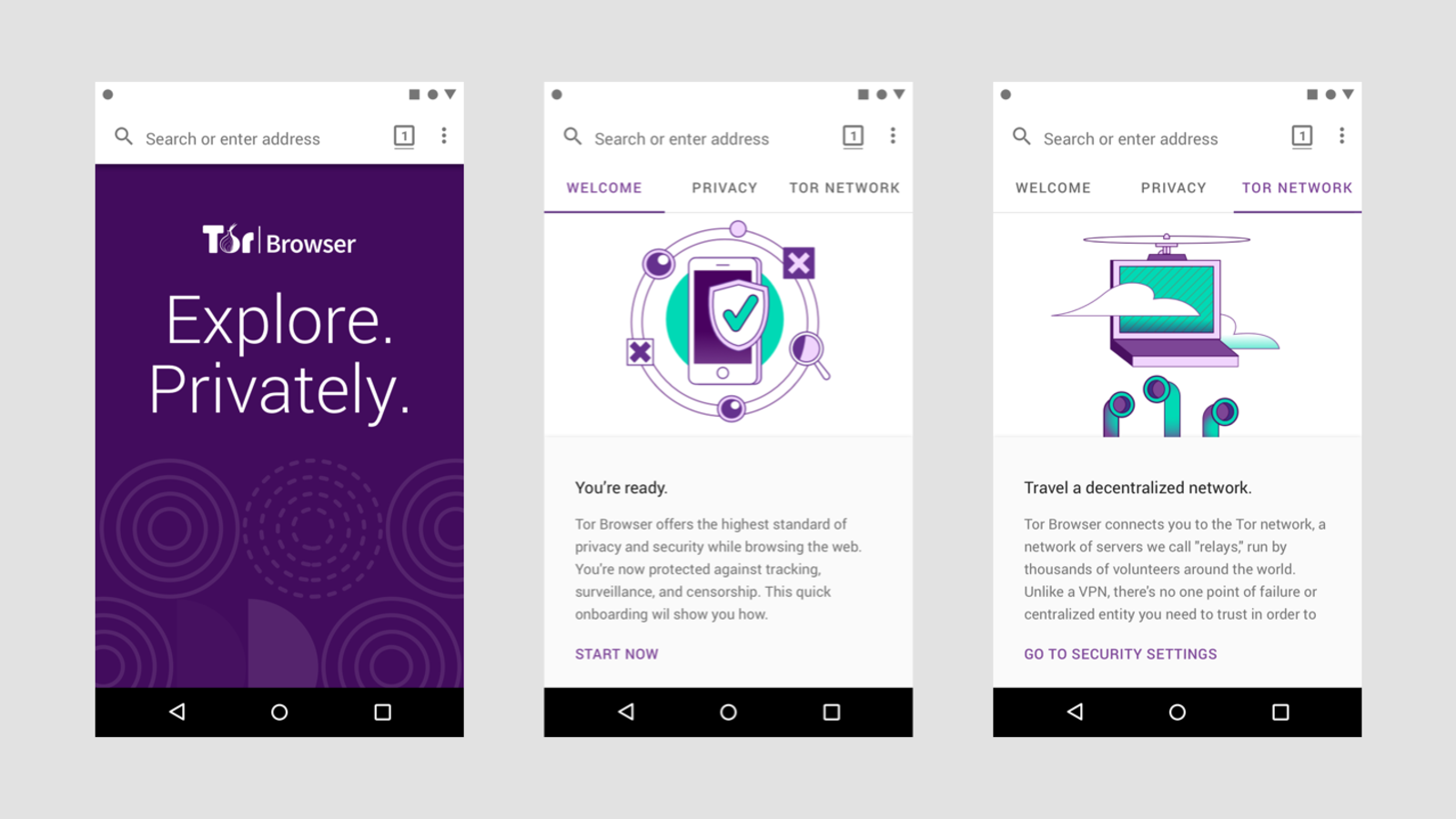
Tor
Tor is a specially modified version of Firefox combined with a peer-to-peer network of volunteer computers. It’s the product of military development but is completely independent and transparent. “Tor” is short for “the onion router”. This refers to the special type of encryption method it uses. Data is not compressed once but wrapped up in multiple layers of encryption. Like onion layers. Data moves from your computer through a random path of volunteer nodes. At each step, another layer of encryption is stripped away until the data leaves the exit node and reaches the destination server. None of the volunteers know where the data originally came from or where it’s going.
Tor is a great privacy tool, but it’s no good for things like streaming video or lag-sensitive applications. It should only be used for basic browsing and sending messages that are very sensitive.
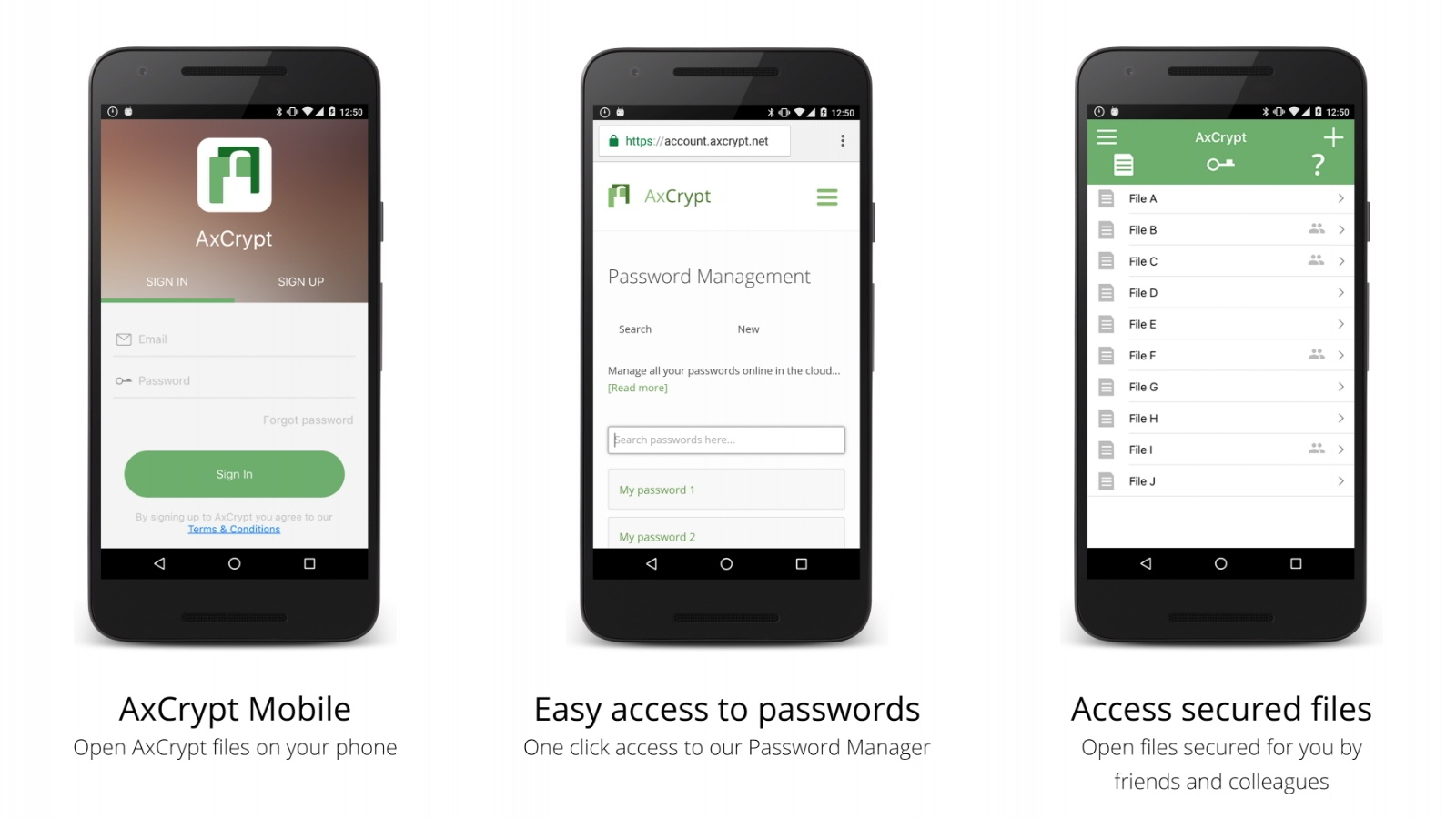
AxCrypt
Axcrypt offers a free product as well as a paid tier. It’s a file encryption tool that also offers password management functionality. AxCrypt has been around since 2001 and is quite popular as far as free encryption tools go. The free PC version offers only AES-128 encryption for your files, with the 256-bit level reserved for paying customers.
You can’t use the software without an online account. For some people that could be a problem. The free Mac version of the software is only a viewer, which makes it useless for anyone who wants to encrypt files. For PC users this is a great addition to the toolbox.
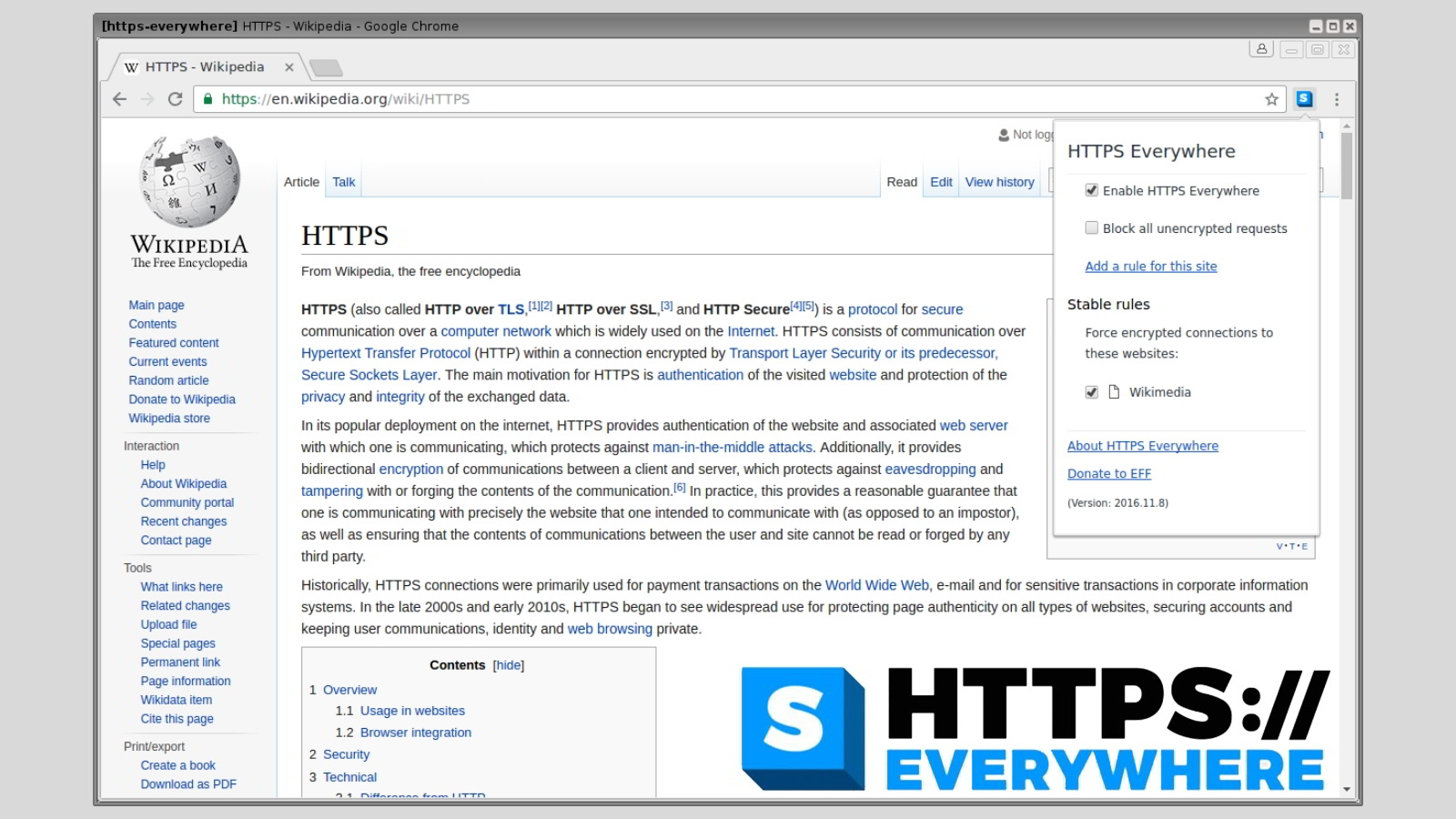
HTTPS Everywhere
HTTPS Everywhere is a browser plugin created by the EFF. When you visit a site that is not secured with HTTPS encryption, this plugin will bridge the gap, making sure that all data packets passing between you and the site can’t be read by third-party spies. Regardless of how you use the internet, this is a plugin you should install just to be safe. The number of sites that don’t use HTTPS is shrinking by the day, so perhaps it won’t be needed forever.
Right now, however, HTTPS Everywhere is rather essential. Just remember that, just because you’re using the platform, doesn’t mean that the owners of the site you are visiting can be trusted!
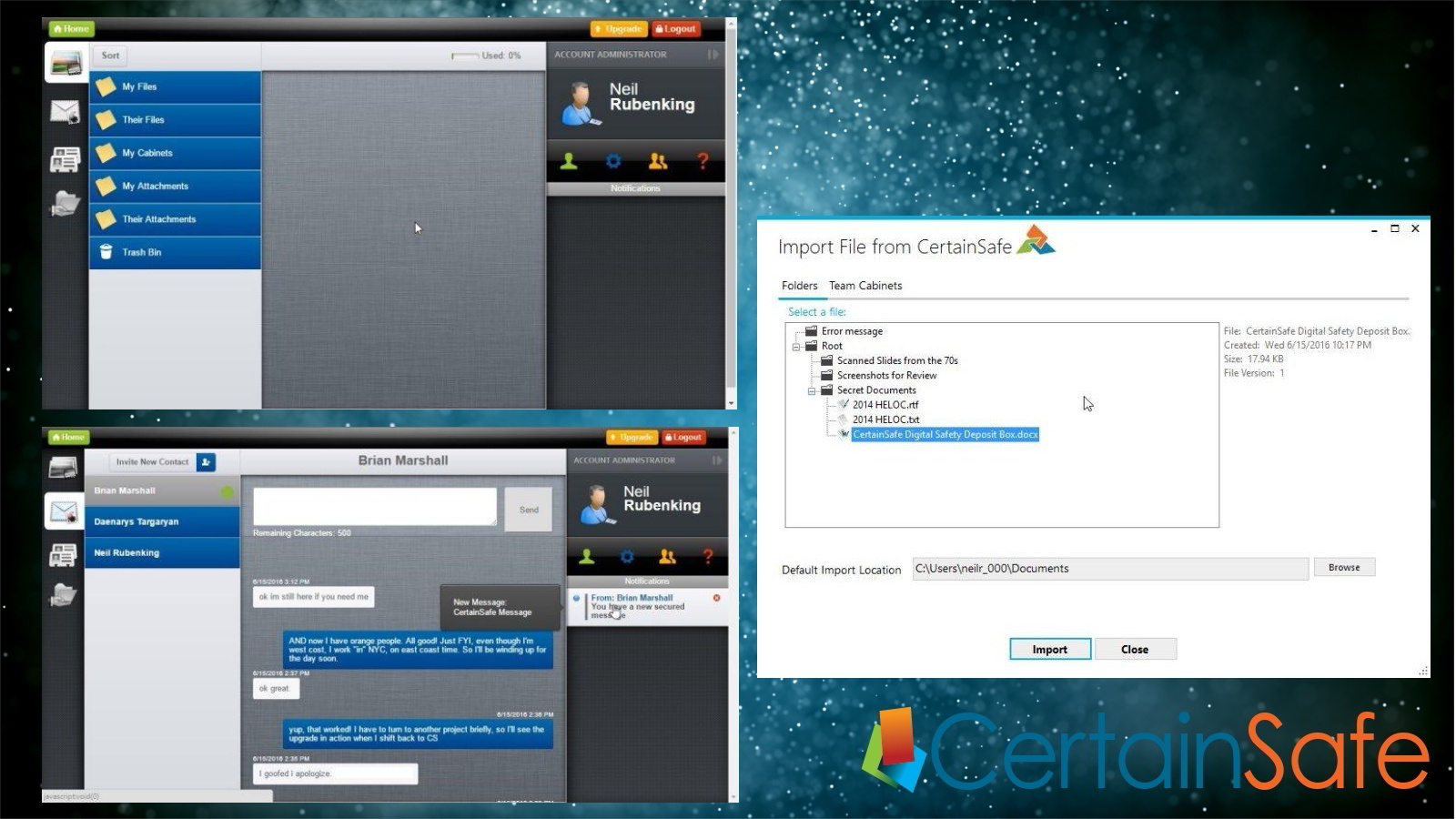
CertainSafe
CertainSafe is a securely encrypted cloud storage tool build to aggressively protect your data. This is a paid service which uses a powerful split-key approach to encryption. You have part of the key and they have part of the key. This means that no decryption can happen without both coming together. CertainSafe can’t look inside your files. If either key part is stolen, the thief will still be unable to decrypt your data. CertainSafe goes even further, using a method known as MicroEncryption. Your data is sectioned into pieces, which are all stored on separate drives and servers. So if a data breach happens on one server, no hacker can get the whole file to decrypt.
The standard tier costs twelve bucks per user and provides 100GB of secured storage. That’s not as much as you’d get from someone like DropBox, but they don’t offer nearly this level of security.
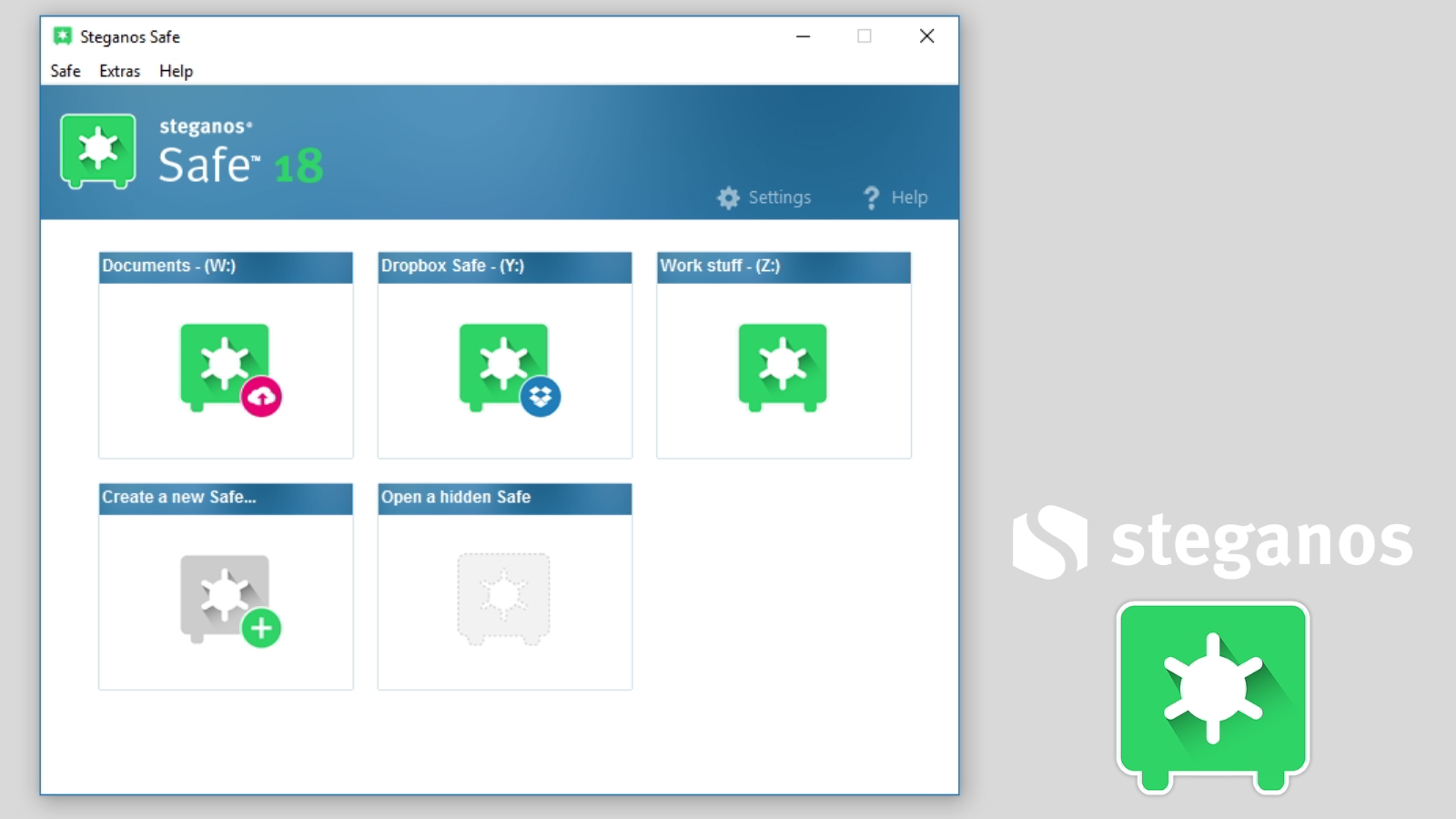
Steganos Safe
Not everyone wants to encrypt their entire hard drive or even let on that they have encrypted anything at all. Which is where a program like Steganos Safe comes into play. With a copy of this software installed, it becomes possible to create a safe area on your drive where you can put seriously secret and sensitive files. Steganos also provides hidden containers, so that someone who steals your computer or hacks into it won’t even know you have protected files on the system. Steganos also provides secure deletion functions, so that sensitive files can’t be retrieved with data recovery tricks.
The only real downside to the program is that you need a copy of it on every computer you want to move files in between. So it’s not the most convenient solution for data encryption on the go.
The other problem is that the program does its job too well. If you lose your access credentials, the data might as well have been deleted. Like most powerful tools, you should exercise caution when using it.
The Right Tools for the Job
It can seem daunting to integrate encryption into every aspect of our lives, but as you can see there's a tool for every use case. Nothing is more important than your privacy when using a computer or the web. So the least you can do is invest a little time and money to make stealing your information much, much harder. I know I sleep better at night knowing my private information is safe. Now you can too.