Belkin’s Wemo Insight Smart Plug May Be the Next Big Malware Target
- Belkin’s Wemo Insight is still plagued by the same zero-day vulnerabilities that were disclosed a year ago.
- The product is no longer available for sale, but many people are still using it, risking their networks.
- Recent samples of the Bashlite malware have incorporated modules that target the Wemo UPnP protocol.
About a full year ago, McAfee disclosed a remote code execution vulnerability in Belkin’s Wemo Insight smart plug and even released a proof-of-concept code that demonstrated the exploitation method as well as the propagation of the compromise. Belkin patched the affected products that were on sale, as well as others in the range that was vulnerable to the same flaws, but the “Wemo Insight” was just retracted from the market with the company ending its support for it. Long story short, those who are stuck with the “Insight” are risking their security, and this risk is about to get a lot greater.
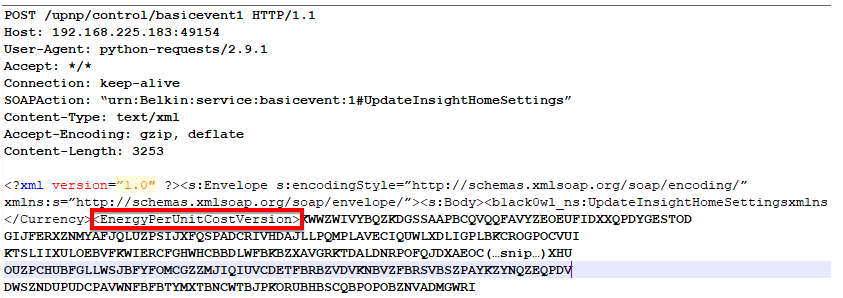
As the McAfee researchers warn, the recent samples of malware that were retrieved from the cyberspace are deploying the “Metasploit” module, which is targeting a known vulnerability in the Wemo UPnP protocol. By analyzing a rich set of “Bashlite” malware samples, the researchers discovered that these malicious tools are actually targeting multiple IoT devices, checking for a large number of known vulnerabilities and checking for default credentials. This automated “scanning and poking” action streamlines the exploitation process. Besides the Belkin products, Bashlite was found to have the hardcoded credentials required to target and exploit many routers of the Alcatel Lucent vendor as well.
image source: securingtomorrow.mcafee.com
Devices like the Belkin Wemo Insight are network linkages, and the chain is as strong as its weakest link. Don’t think that a mere smart plug that monitors your home energy usage isn’t enough to cause network-wide trouble, and don’t treat IoT devices with negligence. The Wemo Insight plug is still paired to your Google Home or Amazon Alexa, connected to your Android or iOS device, and of course to your WiFi. Always apply the rolled out patches as soon as they become available, and monitor the status of the support that the manufacturer of your products are offering. Malicious actors and malware authors are specifically targeting the devices that are left to their fate, and any available exploitation code examples only make their work easier. If you are still using a Wemo Insight smart plug, unplug it, buy a new product, and just forget about it.
Have you ever experienced a network compromise incident due to an unprotected smart plug? Share the details with us in the comments section below, and help your friends stay protected by sharing this post through our socials, on Facebook and Twitter.