Avast Warns About Privacy Flaws in Child Tracking Devices
- Avast researchers find multiple vulnerabilities that scourge China-made GPS trackers.
- The researchers were able to send commands to remote devices after getting their IMEI and API instructions.
- This is not the first time that we see insecure Chinese trackers that can serve as eavesdropping tools.
Researchers of the Avast Threat Labs have discovered multiple severe security vulnerabilities that plague 29 models of child tracking devices made by Shenzhen i365 Tech. The particular Chinese manufacturer is one of the most successful and popular in the field, and they don’t limit themselves to the local national market. Instead, their products are widely available worldwide and are being sold through large marketplaces such as Amazon.com.
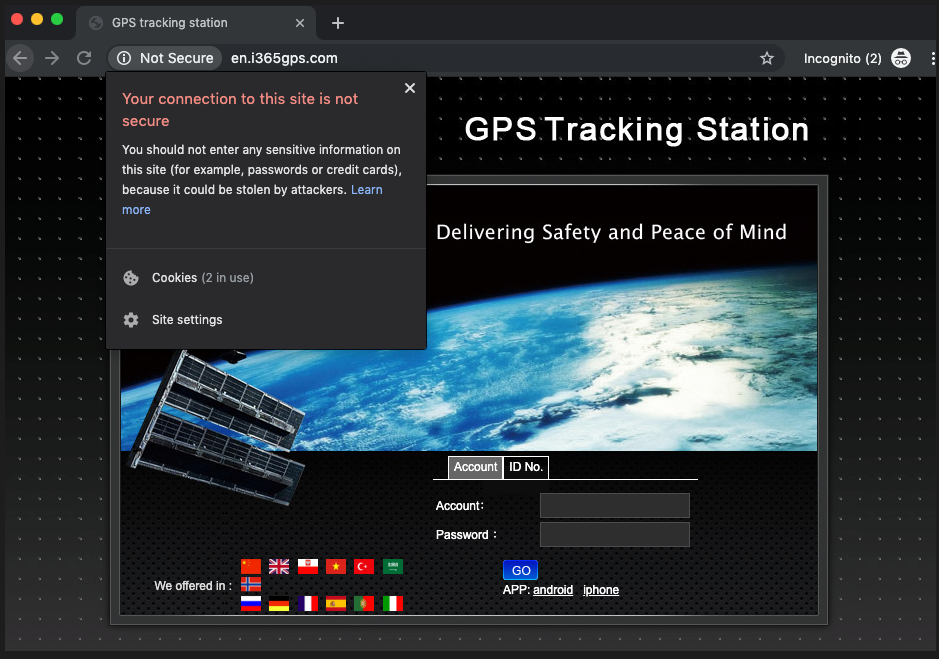
As the researchers claim, the first tracker that they analyzed was the “T8 Mini”, which came with a companion mobile app that is downloaded from an unsecured website. This essentially exposes the sensitive information of the users who register for a new account there. The user is assigned an ID number and a default password of “123456”, which is a comical practice these days. Furthermore, design flaws in the trackers make it easily possible for an attacker to spoof or fake the user’s GPS coordinates, or access the microphone for eavesdropping purposes.
Source: https://decoded.avast.io
The researchers discovered that there are various API endpoints that are used by multiple vendors, figuring out the various “Get” commands that they could pass to the target device. Spoofing the location is done via “GetDeviceLocation”, while for pendants that feature a camera there’s even a “GetDevicePhoto”. By scanning 1 million IMEIs of vulnerable trackers, the team has found that 231k of them were still using the default “123456” password, and 167k were locatable. There were 29 different models made by Shenzen but possibly carrying a label with various other brands.
Source: https://decoded.avast.io
Avast researchers informed the tracking device manufacturer about the security flaws that they found in their products, but after quite some time they have not heard back from them. Thus, the problems are disclosed to the public, so that parents are taking a more responsible approach when they’re out on the market for a child tracker. After all, people are using these devices for safety, but the aforementioned flaws actually introduce new risks for their children.
This is a very similar story to the one that we covered in May, where another GPS tracking emergency pendant was traceable and could also serve as an eavesdropping device. In that case too, an attack would be based on the use of a default weak PIN, IMEI fetching via SMS, and insecure API calls that give a remote actor the power to access the GPS sensor, the microphone, or even reset the device to its default settings.
Are you using a GPS tracker? Do you feel comfortable about its security? Let us know in the comments down below, or on our socials, on Facebook and Twitter.