American Express Customers Fall Victims to a Novel Phishing Attack
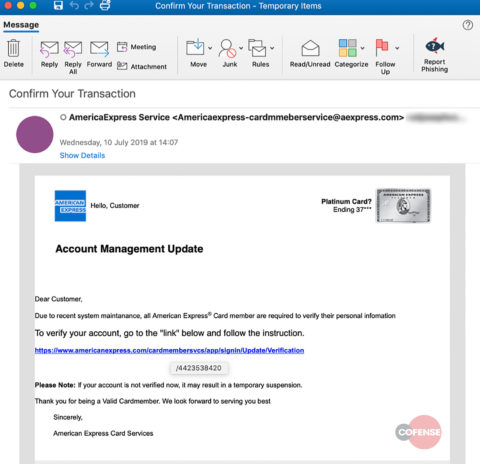
- A new phishing campaign that hides the landing URL inside a hyperlink is targeting American Express customers.
- The card holders are urged to provide their login credentials, allegedly because the system is going through a maintenance session.
- No card issuing authority would ever send an email like that, asking their client to re-enter their credentials.
As discovered by researchers at Cofense and reported by BleepingComputer, there’s a novel phishing attack out there that is trying to steal credentials from American Express customers. This campaign seems to be targeting both corporate and consumer cards, and features the usual typos and grammar errors that are to be found in phishing emails. The difference and the pioneering element lies in how the phishing URL is delivered, hiding it through the use of an HTML element and rendering its detection from antispam solutions impossible, at least for now.
image source: cofense.com
The message of the mail informs the recipients that American Express is going through a system maintenance and needs their card holders to verify their personal information again. Moreover, the message warns the card members that if they don’t verify their accounts right now, they will end up getting a temporary suspension. On that message, there’s a legit-looking clickable hyperlink that features the “https” protocol and the correct “americanexpress.com” URL. This, however, contains an embedded “base href” that leads to “http://wasserhahnonlineshop.de” and then the stitched “/4423538420” which makes up for the full phishing page address. This trick allows the actors to fly under the radar of URL scanners, and get passed through URL filters and gateways.
image source: cofense.com
So, if the victim doesn’t notice where they ended up, they will land on a carefully crafted American Express login portal that includes “account verification” for personal cards, small business cards, corporate cards, and gift card owners. Cofense researchers also confirm that the sample emails that they found were in an environment using Microsoft’s Office 365 Advanced Threat Protection, so the gateway control is not working as expected against this campaign.
image source: cofense.com
American Express customers are very often finding themselves in the center of the phishing cyclone, and high-value targets are more likely to be targeted by novel campaigns. Back in March, we reported about another well-crafted campaign that targeted American Express card holders, asking them to provide their login credentials to re-authenticate again. Attached on the emails were forms using the American Express icons, official colors, and everything that would make them look convincing. The forms asked for quite a lot of sensitive information from the recipients, including their mother’s names, and even the PIN of the cards.
Have something to say on the above? Feel free to do so in the comments down below, or on our socials, on Facebook and Twitter.