Amazon Bans Infamous Kindle Direct Publishing Abuser
- Amazon has banned one of the biggest abusers of the Kindle Direct Publishing system.
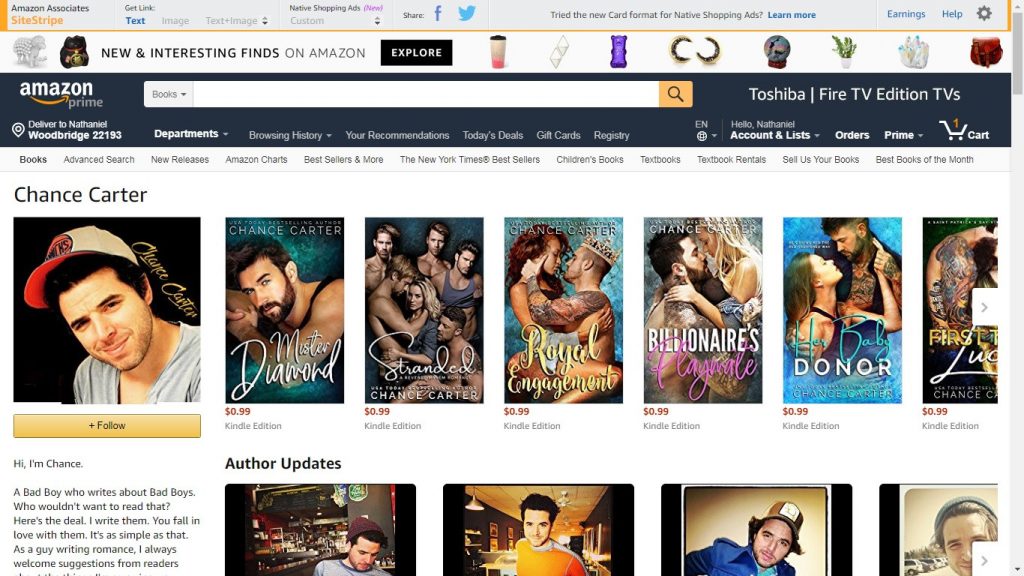
- Chance Carter took advantage of the platform to publish books that contained no real content for $15 each.
- Carter exploited a flaw in the Kindle system that allowed him to get paid for users reading his books even if they simply skipped to the end of his publications.
The Kindle Direct Publishing market is known for its exploitable system that allows users to publish books with filler content and make hundreds of dollars a day. Chance Carter, one of the infamous abusers of the system listed multiple books at $15 that includes nothing but filler content.
Carter created multiple novels by plagiarizing content from other sources which also included scam jobs from Fiverr writers. The scammer’s books always included a note on the first page to skip to the end of a book to access a free giveaway. Kindle Direct Publishing allows users to be paid based on the number of pages read instead of considering factors like reading time. Each time a book is skipped to the last page, it is marked as ‘read’ by Amazon’s system simply based on the number of maximum page number reached. This exploit allowed Carter to make up to $20 each time a reader would skip to the last page of his book, allowing him to con a large number of Kindle users.
Image Courtesy of Amazon
Carter is just one of many scammers who prey on readers on the platform. While Amazon has actively prevented similar scams from running amok, this is one of the longest running scams on the platform. The giveaways Carter promised were fake as well, and none of his readers have reported winning any of the listed giveaways.
Amazon has already patched the exploit and does not allow Kindles to register books as read if users skip to the last page. However, readers who have access to non-updated Kindles can still fall for such scams. While these acts are not criminal in nature unless the original copyright holders of plagiarized content hold scammers accountable, it is still an inconvenience that puts a platform like Kindle to disrepute.