AIESEC Data Breach Exposes Information of 4 Million Applicants
- Four million internship applicants see their sensitive personal information fly off to unknown destinations.
- AIESEC responds by saying “this was our mistake, but only 40 applicants were actually exposed”.
- Budget allocation and funding prioritization indicate that AIESEC didn’t focus on data protection and security.
Yet another unprotected ElasticSearch database has resulted in the leak of the personal data of about four million people who applied for an internship at the AIESEC (Association Internationale des Etudiants en Sciences Economiques at Commerciales). The operator of the database is a global platform and non-profit organization that among other things, offers internships to young people who seek for help in studying in one of the 120 countries or 8000 educational institutes and companies that partner with AIESEC.
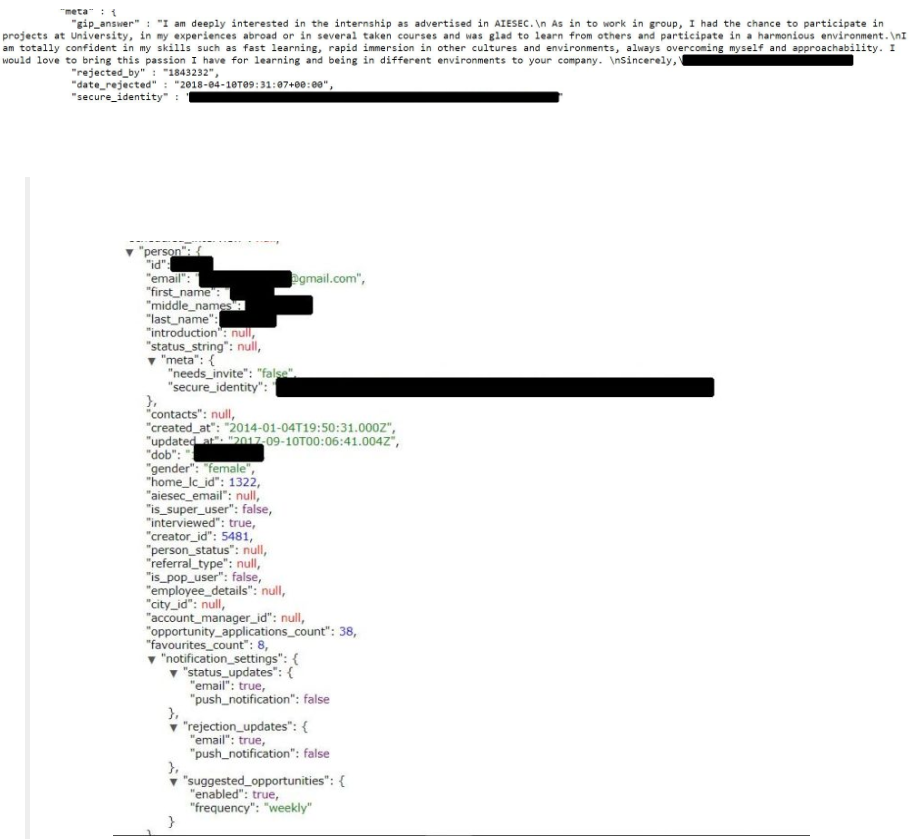
All that said, it is natural to assume that the organization receives many hundreds of internship opportunity applications each month, so protecting the information of the applicants should be a priority for them. Unfortunately, and as revealed by SecurityDiscovery.com researcher Bob Diachenko, this is not the case. The researcher gained access to the personal information of over four million applicants at the AIESEC, including their full names, email addresses, birth dates, gender, etc. What is even more critical is the fact that the unprotected information even includes the details of the interviews with the applicants and the reasons that the applicants gave for the application of the internships. This is the epitome of sensitive information, and by correlating them to the real names, a malicious party could have valuable data in their hands.
Image Source: http://securitydiscovery.com
The three indexes found in the particular ElasticSeach database contain the data of the applications that were submitted on the 2nd half of 2017, and both halves of 2018. AIESEC was quick to respond to the incident, claiming that only 0.001% of the application's data was actually exposed. As they went on to explain further, the particular vulnerability was introduced when their IT was evaluating the implementation of certain improvements for the cluster, leaving the indexes unsecured by mistake. Still, AIESEC promises to inform all of the applicants that were affected, as per the GDPR (General Data Protection Regulation) protocol.
As is often the case in similar incidents, the owner and manager of the database do not pay much attention to the cybersecurity aspect of their operations. Characteristically, and according to AIESEC’s own financial report, their IT budget was only 3.8% of their total salary expenditures. This budget allocation is indicative of the level of attention that AIESEC pays to the IT security sector, and how serious data protection is taken by companies that collect and store sensitive personal information, something that should be their primary priority.
Do you consider the incident as an unavoidable result of data management complexity, or do you think it could have been easily prevented by simply following “the basics”? Let us know of your opinion in the comments below, and don’t forget to also share your thoughts with our online community on Facebook and Twitter.