Sicarii Ransomware: A Deceptive New Ransomware-as-a-Service Threat Using Hebrew Iconography
- Deceptive Branding: Sicarii is a new RaaS that surfaced in late 2025 with explicit Israeli and Jewish branding, despite evidence suggesting non-native Hebrew speakers.
- Geographic Evasion: The malware includes a unique geo-fencing mechanism that actively checks for Israeli system configurations to prevent execution on local devices
- Technical Capabilities: It features AES-GCM encryption, advanced reconnaissance tools, CVE-2025-64446 exploitation capabilities, and data exfiltration mechanisms.
The newly identified Ransomware-as-a-Service (RaaS) group Sicarii has emerged, presenting a unique anomaly in the cybercrime landscape. It overtly aligns itself with Israeli and Jewish symbolism, but cybersecurity analysts caution that this branding may be a performative tactic rather than a genuine ideological stance.
Check Point Research (CPR) Intelligence indicates that while the group uses Hebrew iconography, their underground communications are conducted primarily in fluent Russian, with Hebrew content appearing to be machine-translated.
Technical Sophistication and Data Exfiltration
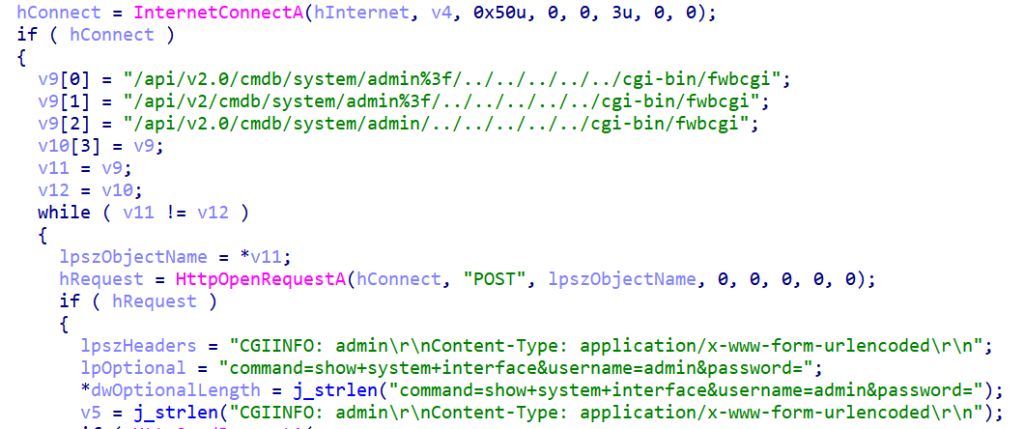
The Sicarii ransomware demonstrates significant technical competence typical of modern cybersecurity threats. Upon infection, the malware performs environment checks to detect sandboxes and virtual machines (VMs), and:
- enumerates the local network configuration,
- maps nearby hosts via ARP requests,
- actively probes discovered systems,
- scans for exposed RDP services and attempts to exploit CVE-2025-64446 on Fortinet devices.
It then initiates a comprehensive data theft process, harvesting credentials from platforms such as Discord, Slack, Roblox, Telegram, Office, WhatsApp, Atomic Wallet, as well as system files. The ransomware also registers a destruct.bat script to execute at system startup that corrupts critical bootloader files, leveraging built-in Windows utilities to perform disk-wiping operations.
The report mentions that an operator posing as Sicarii’s communications lead made some self-reported operational claims in private communications, alleging that Sicarii:
- Compromised 3–6 victims within approximately one month, and all paid the ransom.
- Focuses on small businesses, intentionally avoiding large enterprises and government entities to reduce scrutiny and pressure.
- Is comparable to established Russian ransomware groups such as LockBit and Qilin, but is deliberately maintaining a lower profile “for now.”
A Sicarii operator Telegram account’s profile image features an image associated with the banned Israeli extremist organization called Kach.
Implications for Cyber Defense
The emergence of Sicarii highlights the evolving complexity of attribution in cyber warfare. Furthermore, the inclusion of a destructive component indicates a potential shift from pure extortion to systemic disruption.
Reports this week announced the emergence of a new threat, as the novel Devixor malware combines a banking RAT and ransomware, targeting Iranian banks and crypto platforms.