North Korea’s IT Worker Scheme Expands Beyond US Tech to the UK, Canada, Germany
- Broadening targets: North Korean IT workers are expanding their illicit employment efforts to a wide range of global industries.
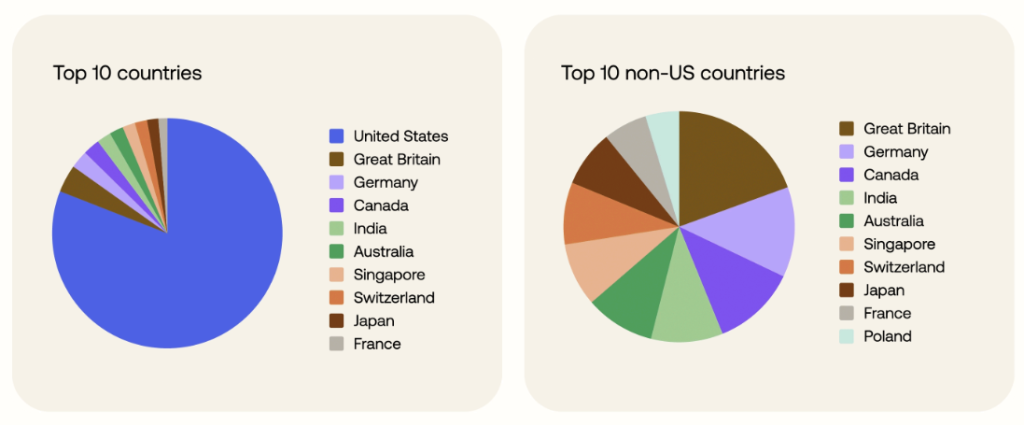
- Global reach: While the U.S. remains the primary target, 27% of targeted entities are based in other countries, including the U.K., Canada, and Germany.
- Affected industries: The scheme now affects industries such as finance, healthcare, public administration, and professional services.
The North Korean IT worker (ITW) scheme has expanded significantly, posing a threat to nearly every industry that hires remote talent. The primary objective remains financial gain for the heavily sanctioned DPRK regime, but the access gained also presents a considerable cybersecurity threat.
While previously focused on major U.S. technology companies, this global industry infiltration now includes finance, healthcare, and government sectors in a growing number of countries.
DPRK Remote Employment Scheme Goes Global
A large-scale analysis by Okta Threat Intelligence identified over 130 fraudulent identities associated with thousands of job interviews across more than 5,000 companies. The findings show a clear diversification of targets.
Only half of the targeted entities were in the information and technology sector. Industries such as financial services, medical technology, and even public administration are now consistently in the crosshairs.
Geographically, the operation is also widening. Although US-based firms still account for the majority of targets (73%), a substantial portion (27%) is located in other developed nations, including the U.K., Canada, and Germany.
Okta said this indicates a strategic shift to exploit hiring markets that may be less aware of this specific threat.
Evolving Tactics and Security Implications
The DPRK remote employment scheme has matured, with workers using identity fraud and local facilitators to secure positions. The threat actors are increasingly applying for a variety of remote roles, from software engineering to back-office financial processing.
This infiltration creates significant risks for businesses, including sanctions violations, data theft, and the potential for corporate networks to be used for future cyber operations.
Organizations are advised to strengthen identity verification processes during recruitment and monitor for anomalous behavior from remote workers:
- Strengthen applicant identity verification
- Tighten recruitment and screening processes
- Enforce role-based and segregated access controls
- Monitor contractors and third-party service providers
- Implement insider-threat and security awareness programs
- Coordinate with law enforcement and industry peers
- Conduct regular risk assessments and red-team exercises
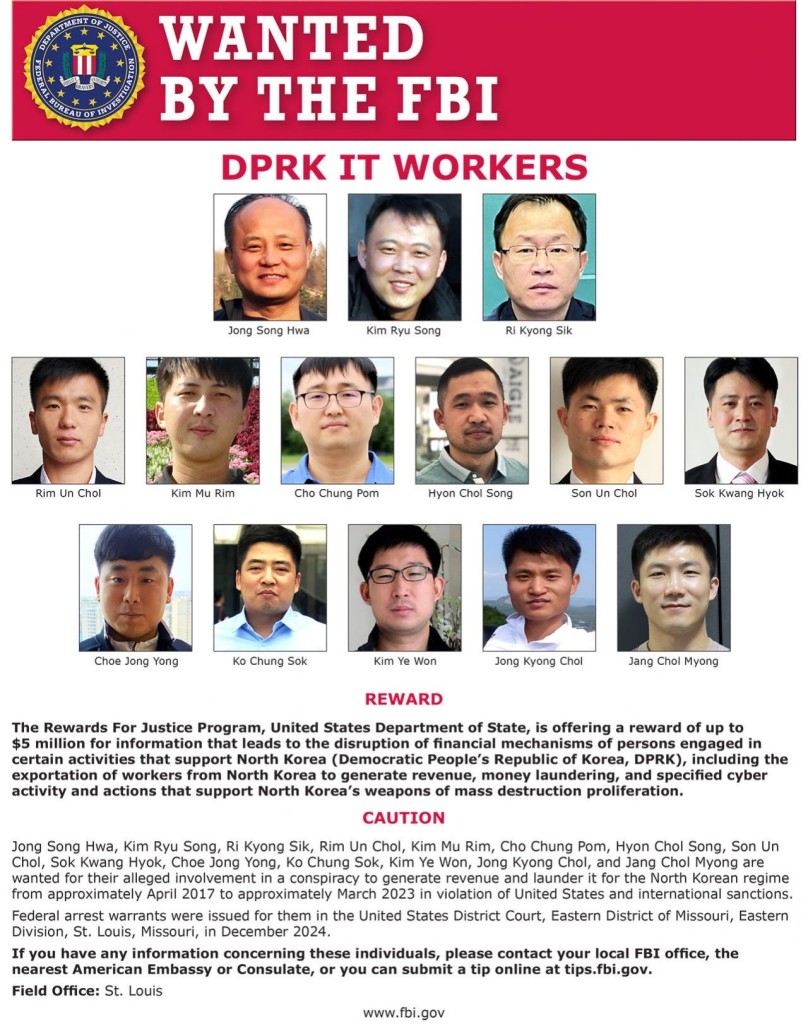
In August, the U.S. Treasury sanctioned two individuals and two entities linked to the IT worker scheme network funding North Korea's weapons programs, and CrowdStrike reported North Korean spies had infiltrated over 320 companies via GenAI-backed remote work scams.