JSCEAL Malware Targets Crypto Apps in Sophisticated Campaign Leveraging Facebook Ads
- Stealing user data: A novel phishing campaign targets credentials and crypto wallet details by impersonating legitimate brands through websites.
- JSCEAL malware: The actors leveraged Node.js to launch a compiled JavaScript malware.
- Impacted users: Researchers estimated that millions of users in the EU saw approximately 35,000 malicious ads on Facebook.
A new and sophisticated cyber threat, JSCEAL malware, was seen targeting cryptocurrency application users. The campaign utilizes advanced techniques to steal sensitive user data through fake websites, primarily promoted via Facebook advertisements.
Tactics of the JSCEAL Campaign
The JSCEAL malware leverages malicious advertisements to lure users into installing fake cryptocurrency trading applications, impersonating nearly 50 reputable crypto platforms like Binance and Revolut.
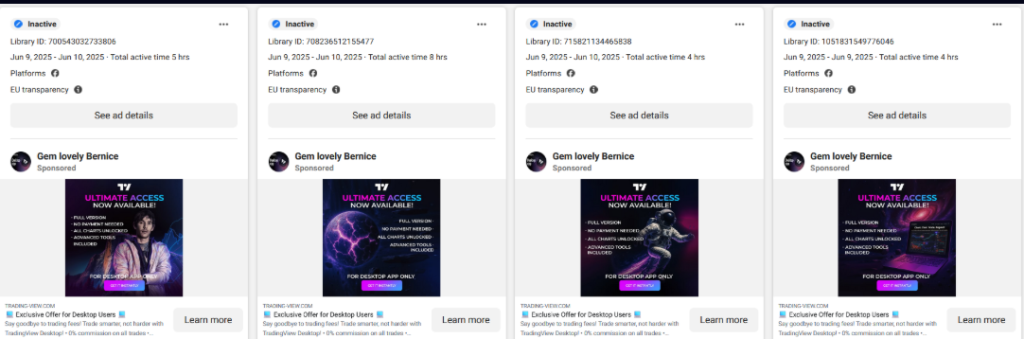
Check Point Research (CPR) uncovered that during the first half of 2025 alone, approximately 35,000 deceptive advertisements garnered millions of views across the European Union.
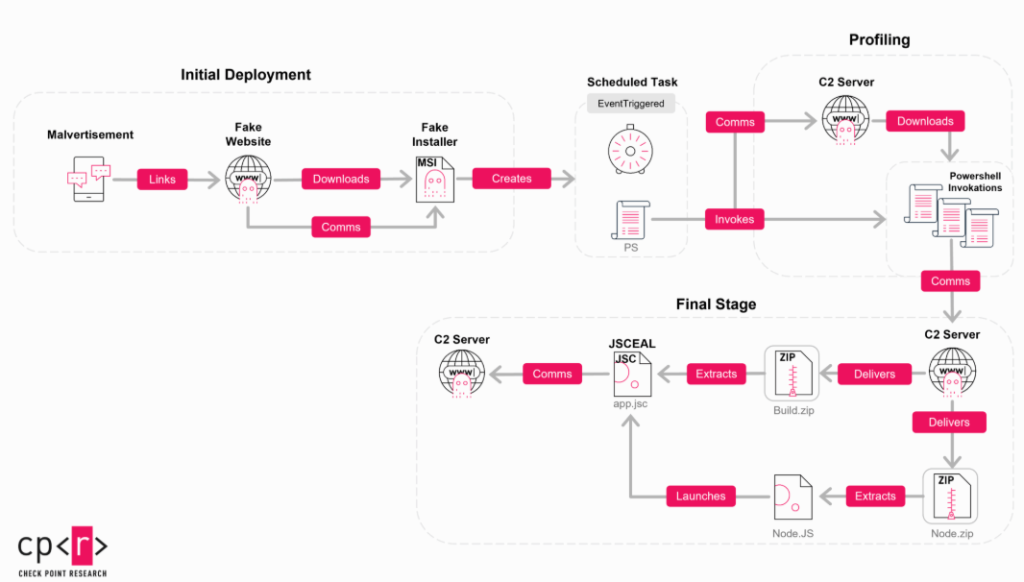
The infection process is highly modular, using Node.js-based compiled JavaScript (JSC) files.
This multi-layered approach involves redirection chains from malicious advertisements to landing pages hosting infected MSI installers. Once executed, these installers initiate staged attacks, including detailed machine profiling and deployment of malware payloads designed to steal crypto assets and user credentials.
A unique mechanism was implemented, which requires the malicious site and the installer to run simultaneously for successful execution. The threat actors also use decoy websites if the target’s IP address is not within the desired range or the referrer is not Facebook.
The malware also implements advanced anti-detection mechanisms, such as script-based fingerprinting and obfuscation techniques. Notably, it uses compiled V8 JavaScript to bypass static analysis tools.
Protecting Against JSCEAL
CPR emphasizes vigilance for all crypto users and institutions. Recommendations include verifying app authenticity, using advanced threat prevention tools, and avoiding suspicious advertisements.
Fake websites that impersonate brands to distribute malware like JSCEAL are not new. In the latest news, a phishing campaign leveraged fake Microsoft 365 login pages for BEC scams and a malicious Telegram APK campaign exploits fake domains and Android vulnerabilities.