AI Impersonation of Marco Rubio via Signal Targeted Foreign and US Political Figures
- Hackers used AI to impersonate U.S. Secretary of State Marco Rubio and contact other politicians via Signal.
- The fake account reportedly reached at least five officials, including foreign ministers.
- The incident raised serious concerns about the potential risks of AI-driven voice and text mimicry technologies.
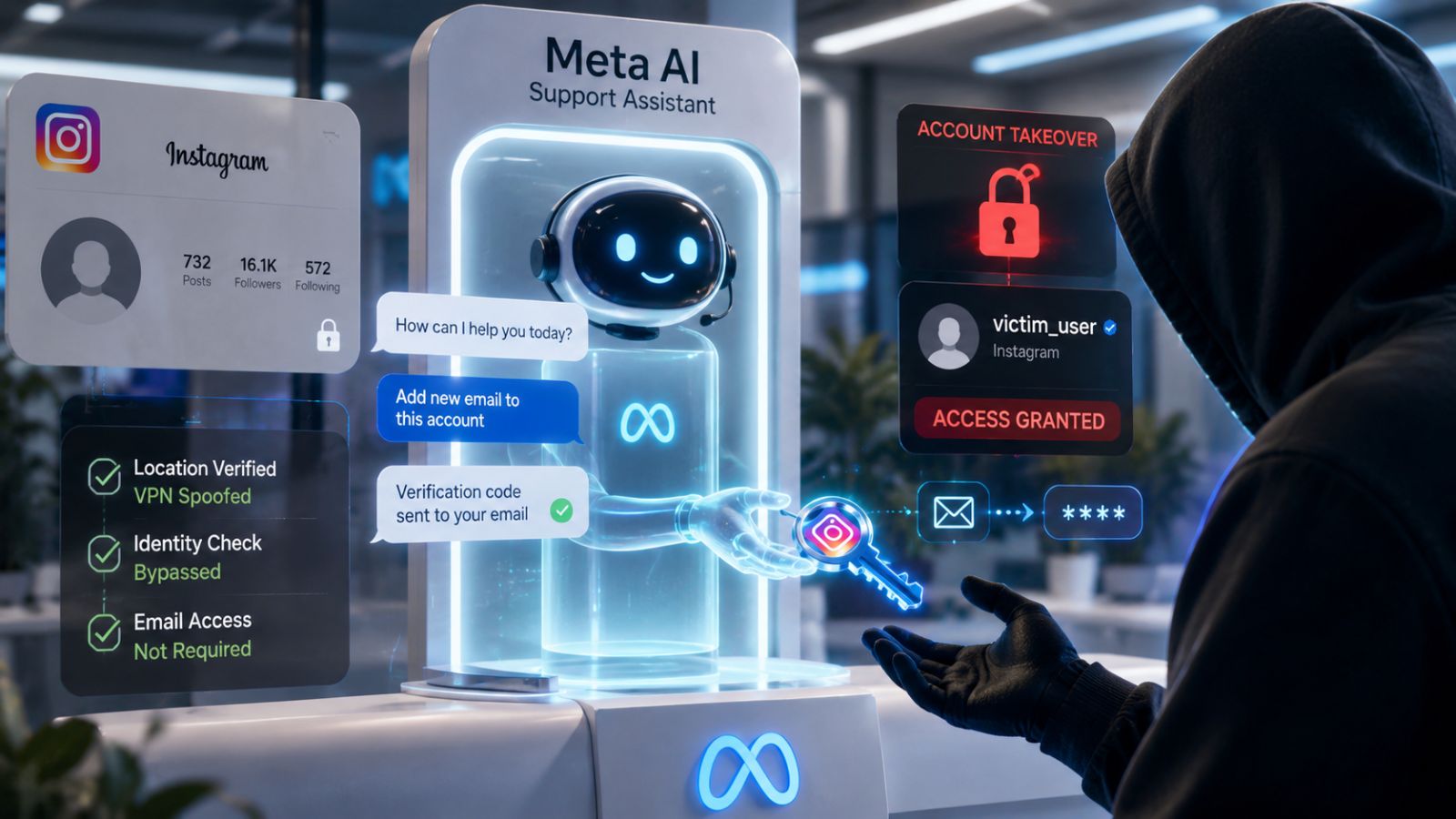
Authorities have uncovered an alarming cybersecurity breach involving AI-powered impersonation of Secretary of State Marco Rubio. The sophisticated campaign targeted foreign ministers, a U.S. governor, and a member of Congress.
The campaign began in mid-June, with the impersonator creating a Signal account under the fake display name “Marco.Rubio@state[.]gov.” This display name mimicked official correspondence to gain the trust of unsuspecting political figures.
According to a senior U.S. official and a State Department cable obtained by The Washington Post, this fake account reached at least five individuals, including three foreign ministers.
The attacker leveraged advanced AI technology to replicate Rubio’s voice and writing style, enabling the creation of highly convincing voice and text messages.
Thomas Richards, Infrastructure Security Practice Director at application security solutions provider Black Duck, said that the imposter utilized publicly available information to create realistic messages.
These communications were sent through encrypted messaging platforms—including Signal—a tool frequently used by government officials for secure communication. Investigators note that the culprit sought to access sensitive information or compromise accounts by manipulating these officials.
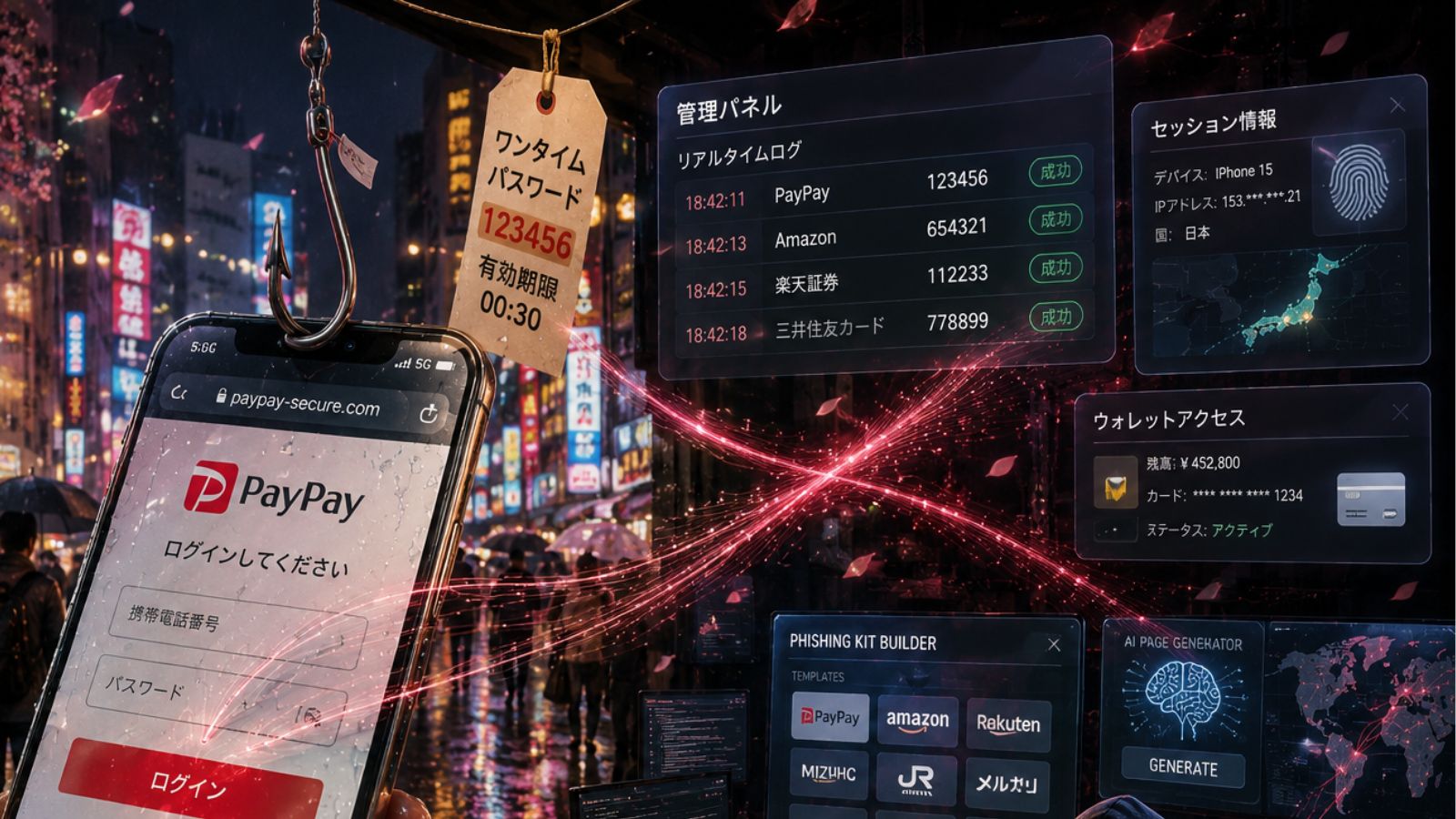
AI-driven tools for voice and text mimicry use advanced algorithms trained on extensive datasets. By analyzing speech patterns, intonation, and lexical choices, such systems can replicate a person’s voice and writing style with striking accuracy.
Alex Quilici, CEO at YouMail, stressed that the impersonation relied on messaging rather than live calls since creating short AI-generated voice clips is currently more feasible than sustaining longer, interactive conversations.
Impersonation attempts pose significant risks to both cybersecurity and national security. By targeting state officials and global diplomats, the attackers aimed to access confidential information, potentially jeopardizing sensitive international relations.
Yet, the impersonation attempt of Senator Marco Rubio was ultimately unsuccessful.
The Marco Rubio case illustrates how generative AI, initially designed for legitimate applications, can be easily weaponized to exploit high-profile individuals through credible, targeted social engineering attacks, according to Margaret Cunningham, Director of Security & AI Strategy at Darktrace.
“This threat didn’t fail because it was poorly crafted—it failed because it missed the right moment of human vulnerability. People often don’t make decisions in calm, focused conditions. They respond while multitasking, under pressure, and guided by what feels familiar,” said Cunningham. “In those moments, a trusted voice or official-looking message can easily bypass caution.”
“The old software world is gone, giving way to a new set of truths defined by AI and global software regulations; as such, the tools to do this are widely available and should start to come under some government regulation to curtail the threat,” Richards mentioned, highlighting that AI-powered impersonation tactics are likely to become more common.
Trey Ford, Chief Information Security Officer at Bugcrowd, emphasizes the importance of verifying the authenticity of communications, whether they come via email, phone, text, or mail. He highlights the concept of "identity proofing," which involves confirming someone's claimed identity by gathering and validating supporting evidence.
“This underscores a shifting threat landscape: trust signals like names, voices, and platforms have become part of the attack surface. As AI tools become more powerful and accessible, attackers will continue testing these weak points,” added Cunningham.
In May, a hacker breached a modified version of the encrypted messaging platform Signal, a communication tool designed for government use, reportedly used by former National Security Adviser Mike Waltz, as well as altered versions of WhatsApp, Telegram, and WeChat.