8.2 TB Sensitive Data of MobiKwik Users Are Sold on Hacker Forum
- MobiKwik has had an undisclosed security incident as someone is selling user data on hacker forums.
- The massive database comprises ID scans, passports, selfies, emails, phones, addresses, passwords, and a lot more.
- The firm hasn’t released a statement about the leaked data yet, but the exposed users are already at great risk.
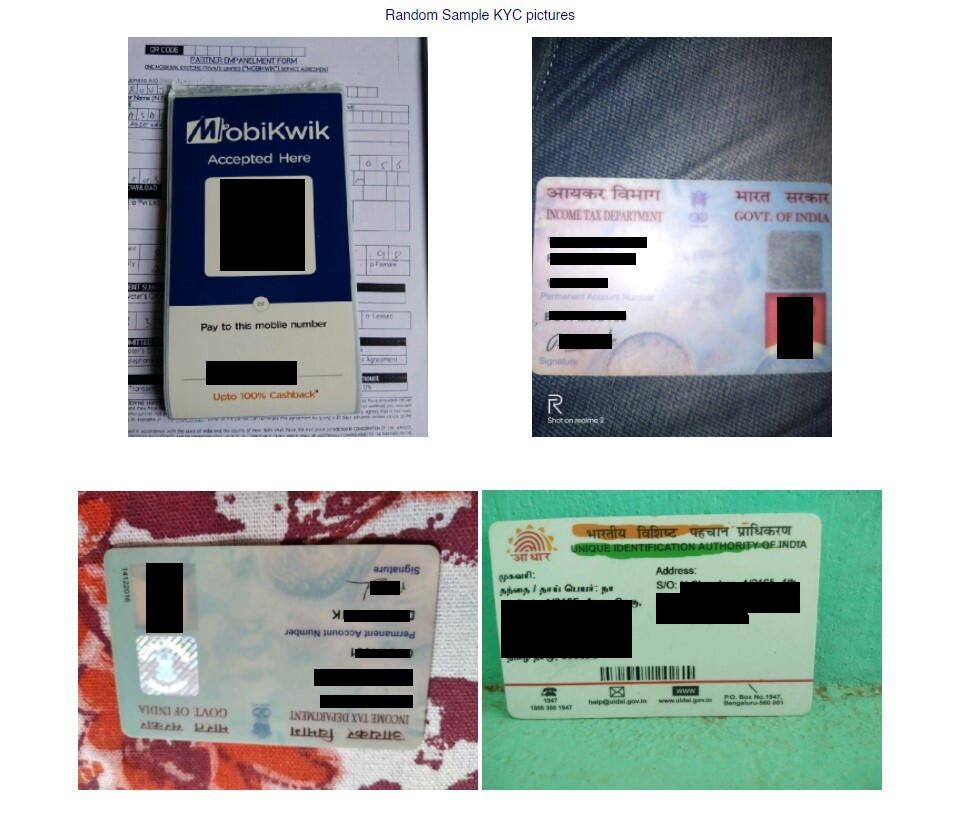
A massive database appeared for sale on a popular hacker forum containing highly sensitive details of millions of Indians, users of MobiKwik. This is a Gurugram-based company offering a mobile phone-based payment system and a digital wallet, enabling users to perform transactions right from the mobile app. From 2016 and onward, MobiKwik even offered small loans to its users, and so KYC requirements had to be put in place. This means that the firm was holding PII, ID documents, scanned passports and Aadhar cards, and a lot more.
Independent researcher Rajshekhar Rajaharia has spotted the new database and informed us of the fact, so we have taken a look, and we can confirm that the data appears to be valid. The seller has set up a dark web portal where one can search by phone number or email ID and get the specific results out of a total of 8.2 TB of data.
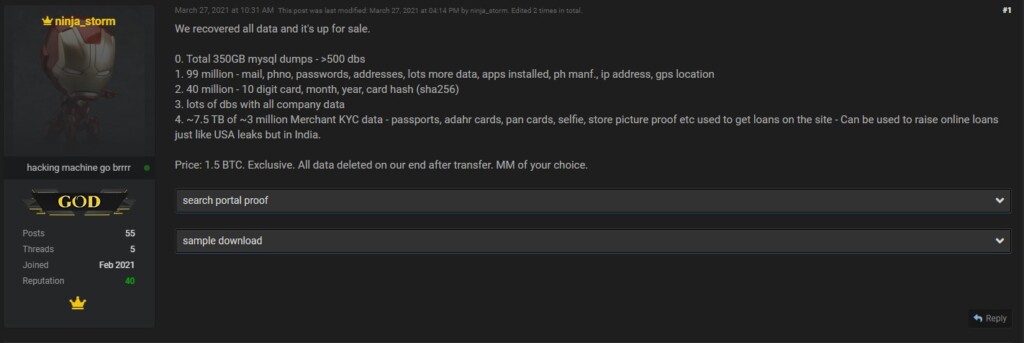
For the set price of 1.5 BTC ($84k), a buyer can get the entire database and have the dark web portal taken offline, keeping everything exclusive. The seller lists the following as included in the massive pack:
- Total 350GB MySQL dumps - > 500 databases
- 99 million – mail, phone, passwords, addresses, lots more data, apps installed, ph manf., IP address, GPS location
- 40 million – 10 digit card, month, year, card hash (sha256)
- lots of databases with all company data
- ~7.5 TB of ~3 million Merchant KYC data – passports, Aadhar cards, pan cards, selfie, store picture proof, etc., used to get loans on the site
The seller claims that each of the merchant entries in the database can be used to raise $500-$1,000 loans in Indian currency, so the investment of the 1.5 BTC could supposedly yield up to three billion USD. Allegedly, a partner has tried to raise a couple of loans as proof of concept, and it worked out as expected.
To avoid paying the full price, someone has set up a script to try and scrape the entire 99 million entries from the Tor site, which obviously is a desperate effort. Still, it goes to show that there’s some interest in this data, even if many question its real value against the price tag. The situation is quite bad for the exposed users as anyone can search them specifically, and some are already scraping parts of the database.
At the time of writing this, MobiKwik is yet to acknowledge any data breaches that resulted in this massive exposure, and the company hasn’t made any relevant announcements on the official site or its social media channels. We have asked for a comment, and we will update this piece as soon as we hear back from them.
Update - March 29: We have received the following comment from MobiKwik:
So, MobiKwik denies that the data which we have seen online belong to them, actually accusing the researcher of having ulterior motives for making these claims. However, they have not explained why the seller is also claiming the source is MobiKwik, and how come the samples that we've seen on the Tor site contain images of MobiKwik QR codes. The story is currently developing; we will update you while we get any additional information on the leak.