What Is a VPN & Why Do I Need It?
"VPN" stands for "Virtual Private Network," which gives you an accurate but somewhat broad definition of the role of today's commercial VPN services. More precisely, today's VPN services can help you bypass censorship, unblock websites, reach new digital services, download torrents, bypass ISP censorship, and optimize your online gameplay experience. Yes, all of that is possible using a single VPN application.
As you can already imagine, VPNs aren't exactly a new thing. VPN history starts in 1996 when a Microsoft employee (Gurdeep Singh-Pall) began his work on PPTP (Point-to-Point Tunneling Protocol). The official specification of that protocol was published in 1999, while the first commercial VPN services started appearing in 2005.
During the last 15+ years, the global VPN industry became a $30 billion industry, expected to reach a market size value of $92 billion by 2027. There are already hundreds of VPN services from all kinds of cyber-sec companies. And, of course, there are some VPN scams as well, as could be expected from such a high-value industry. So, entering the world of today's VPNs does require a certain level of caution.
That said, we'll use this guide to explain what is a VPN, how a VPN works, what you can expect from one, whether VPNs are legal, as well as plenty more. So, let's jump right in!
What Is a VPN?
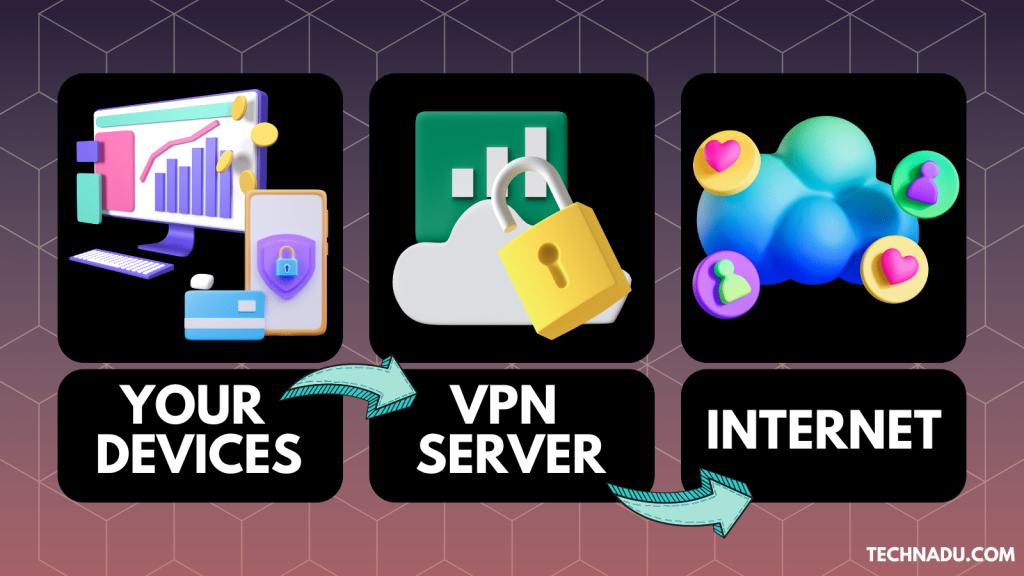
A VPN is a digital service that encrypts your Internet data. Once you connect to a VPN server, your incoming and outgoing Internet data becomes invisible to others on the Web.
Speaking of the need to create secure connections, you might not even be aware that you emit a lot of information that malicious actors would love to exploit.
Some of it is obvious - such as your credit card number, passport details, bank account logins, and so on. That’s why finance-related sites and online services that send and receive sensitive information have special technologies to protect that information.
Your bank should have an address that starts with 'HTTPS' rather than 'HTTP,' which shows that it's secure. No one can 'listen in' when you send your username and password to your bank because the information is written in a special code. In other words, it’s encrypted.
That's great for your bank-specific data, but there’s still a lot of information you broadcast on the Web. It’s not just criminals either. You also must think about privacy-intruding corporations and governments taking part in the 5/9/14-Eyes Alliance.
This is precisely where VPNs come into play. Designed to encrypt your connection, hide your online whereabouts, and make sure no one knows what you do online, VPNs have become the ultimate tool for protecting your online security and privacy.
If you wish to learn more about what can you do with a VPN, as well as who uses a VPN, click the provided links. We're sure you'll be surprised by the capabilities of today's VPN services.
How Does a VPN Work?
A VPN works by authenticating, encapsulating, and encrypting your Web data. In other words, VPNs process your incoming and outgoing Web data by routing it through secure servers. While doing so, your data becomes unreadable to anyone else online.
Sounds complicated? Well, we have a dedicated guide on how a VPN works, but let's give you a brief overview of what happens in each of those 3 steps:
- Step 1 - Authentication: The easiest one to understand is authentication because we all deal with it every day. You have to prove to the VPN that you are really who you say you are. One way VPNs do this is through a plain old username and password.
- Step 2 - Encapsulation: This is the key to how VPNs hide what sort of data you’re sending. They wrap your data packets in their own VPN-specific packets. So, anyone who inspects those packets will see the same VPN-branded data no matter what’s actually in there.
- Step 3 - Encryption: Encryption is the last piece of the VPN puzzle. This is how the VPN scrambles your data so that even if someone analyzes your packets, it won’t make any sense of that data. Without a special key to unscramble the information, it’s all just gibberish, and only you and the VPN have copies of the encryption keys.
All VPNs work the same, in their essence. However, they all use different VPN protocols, some of which are more secure and faster than others. That's why it's imperative to pick a reliable VPN, as that's the best way to avoid VPN leaks.
Is a VPN Legal and Safe?
Yes, VPNs are legal and safe to use - in most countries. More precisely, there's a small group of countries that have either banned or regulated the use of VPN services.
If you check our list of the countries where VPNs are banned, you'll see that mostly totalitarian and authoritarian regimes impose online censorship. However, country-based VPN blocks are practically impossible to implement. For example, even though Russia is trying to ban VPNs, this type of software is on the rise in the country.
In the rest of the world, VPNs are completely safe to use. You have every right to pick any VPN service, become a paying subscriber, and use it to access any website.
We offer a guide that explains how secure is a VPN, explaining the crucial aspects of a capable and trustworthy VPN. So, no matter if you live in a restrictive or free country, going with a secure VPN that you can trust is always a good idea.
What Does a VPN Do?
A VPN can do many things, such as - protect your privacy, secure any Wi-Fi connection, help you work remotely, fight against censorship, and unblock sites. Here's more information:
- VPNs Protect Your Privacy: By encrypting your Internet traffic, VPNs hide your IP address, location-related information, as well as your Web browsing and online activity. Therefore, they ensure your privacy is protected on the Web. Here's what else a VPN hides.
- VPNs Secure Any Wi-Fi Connection: There are many reasons why you should use a VPN at home. However, there are even more reasons to use it on the go. VPNs can make any Wi-Fi network secure and private, even open/public Wi-Fi. So, you won't be targeted by Wi-Fi hotspots designed to collect personal data.
- VPNs Help You Work Remotely: If you switched to working remotely, you now have to think about the privacy of your sensitive information. A VPN can help you establish a data tunnel during your work hours, ensuring your work files don't leak on the Web.
- VPNs Fight Against Censorship: Around the world, censorship is on the rise, with new types of Web roadblocks appearing daily. If you wish to open up your access to the Web, you won't find a better tool for the job than a VPN.
- VPNs Unblock Websites: Among the many reasons to use a VPN, a prominent one is the ability of VPNs to unblock websites. If you want to access geo-restricted streaming services or any website that doesn't work in your country, a VPN will do the trick.
If you wish to learn more, check our central guide explaining what does a VPN do. It would also be useful to check the things you can do with a VPN, giving you a clearer idea of what to expect.
What a VPN Does Not Do?
When it comes to things VPNs can't do, that includes - protecting you from malware, keeping you 100% anonymous online, and stopping cookies from identifying you. Here's more info:
- VPNs Don't Protect You from Malware: Some VPNs come with light malware tools, being able to scan small files. However, they can't stop malware from reaching your device, especially stronger malware breeds. If malware is a concern, check our guide to the best antivirus with a VPN included.
- VPNs Don't Keep You 100% Anonymous: VPNs hide your online data, which means even your ISP won't see what you do online. Still, you still have to log in to services like Gmail, Facebook, Twitter, and similar. By logging in, you accept for those services to track you - until you decide to log out.
- VPNs Don't Stop Tracking via Cookies: Individual websites use cookies for different purposes, like offering location-based services. VPNs can't stop those cookies, as that would prevent those websites from working.
Want to dive deeper into what a VPN does not do? Click the provided link to learn more. You can also check our guide to the biggest VPN myths, for a better understanding of what to expect.
What Is a VPN Used For?
You can use a VPN for many things, the most important of which is - to hide your Web browsing activity, protect yourself on public Wi-Fi, change or hide your IP address, or optimize your gaming sessions. Here's a quick overview:
- Hide Your Web Browsing Activity: As explained previously, the primary purpose of VPNs is to hide what you do online. They're doing that by encrypting your Web connection, making it unreadable to anyone else. That's how a VPN hides your browsing history from your ISP, and it also hides from your ISP what you download.
- Access Geo-Blocked Websites: We already told you that VPNs are great for unblocking geo-blocked websites. That means having access to any foreign news site or any media streaming website that doesn't work in your country.
- Download Torrents: It's essential to hide your torrenting from your ISP. A VPN will protect you when downloading torrents by hiding your IP address. That means your location and address will remain hidden. So, you can download torrents with a VPN anonymously.
- Protect Yourself on Public Wi-Fi: Public Wi-Fi networks are fertile grounds for malicious actors to affect groups of devices at once. As such, most Wi-Fi networks are designed to exploit your private information. So, you can use a VPN on public Wi-Fi to put an end to that.
- Change/Hide Your IP Address: You can use a VPN to change your IP address to one from your or some other country. That way, you can secure your privacy and unblock websites. VPNs are actually the easiest way to hide your IP address.
- Reduce Ping When Gaming: If you're not using a VPN for gaming, you're missing out on a lot. A VPN can help reduce your ping, which means it handles your latency. That leads to more enjoyable online gameplay sessions.
There are a few more possible uses for any capable VPN service. Learn more about those in our guide that explains what is a VPN used for - via actionable tips.
What Types of VPNs Exist?
There are two main types of VPNs: personal VPN services and business VPN services. Let's check out what's different between those two VPN types:
- Personal VPNs: The main focus of this guide is on personal VPNs. You can pick any commercially available VPN, install it on your device, and use it without supervision. That means you can use your VPN to unblock websites, hide your online data (here's the best VPN for privacy, by the way), and more.
- Business VPNs: When it comes to business VPNs, we have site-to-site VPNs. This kind of VPN connection creates a permanent connection between multiple offices. There are also remote access VPNs, which provide a temporary connection between the business' data center and the user's device.
To learn more about the types of VPNs, you can read about who typically uses a VPN. That should show you all the possible scenarios where VPNs can be beneficial.
What Are the Most Important VPN Features?
The most important VPN features to keep in mind are: data encryption, split tunneling, kill switch, data leak protection, and simultaneous connections. Here's more info:
- Data Encryption: All VPNs use data encryption. They use a number of VPN protocols to dictate how rigorously your data is encrypted. If you want the best security, pick OpenVPN. You can go with WireGuard if you need performance. And if you want ultra-tough security, learn about VPN obfuscation and go for a double VPN, encrypting your data twice.
- Split Tunneling: This feature allows you to set up two tunnels. For example, you can have one tunnel for your VPN data, ensuring you download torrents anonymously, for example. At the same time, you can keep a regular data tunnel, giving you access to websites that might block VPNs. If you wish to know more, here's our guide to split tunneling.
- Kill Switch: Your connection to a VPN server can drop at any moment. In that case, your data will leak on the Web, which is important to prevent when doing sensitive tasks online. You can prevent that from happening using a kill switch, which shuts down your Internet connectivity until you're connected to your VPN.
- Data Leak Protection: As mentioned above, your data can leak when your VPN connection drops. However, less secure VPNs can leak your data even through their VPN tunnels. So, it's crucial to pick a VPN with high-end security measures. Learn more about the most common types of VPN leaks, and how to stop them.
- Simultaneous Connections: VPNs typically limit the number of simultaneous connections, which means you can run them on 5 to 10 devices at the same time. So, make sure to pay attention to this VPN feature before buying a VPN. If you need help, you should check our guide to the best VPN for multiple devices.
Premium VPN vs. Free VPN vs. Free VPN Trial
When it comes to the price of VPNs, you can choose from free and premium VPNs. However, many premium VPNs also offer free VPN trials, which is a good way to test those services without any financial risk.
However, those terms can be a bit confusing, so let's explain them a bit better. Check the following table to learn more.
As you can see, it's hard to recommend free VPN services. That's because most free VPNs are not safe, as they're mostly designed to exploit your privacy (here's how to find a trustworthy VPN, by the way). On top of that, they come with strict data allowances and they're usually painfully slow.
That said, we recommend going for a free VPN trial if you're unsure about spending money on a VPN service. By going for the best VPN free trial, you can test your chosen VPN with no limitations. If you change your mind, you'll have your money back - as simple as that.
And if you already know what to expect, make your options broader and go for a premium VPN from the get-go. Our central guide to the best VPN services can help narrow down your list of options, as it features the most capable VPNs only.
We also have a useful tip regarding how to save money. Many VPNs offer occasional promos, lowering their prices in a dramatic way. So, don't forget to check for the best VPN deals, as well as the best cheap VPN services.
To learn more, check our guide that explained the differences between free VPNs, paid VPNs, and free trial VPNs.
Also, if you're willing to spend money on a premium VPN, make sure to spend it wisely. Here's how much does a VPN cost, what to look for in a VPN, and finally - go through our VPN buyer's guide, helping you create your personal set of criteria.
How to Set Up and Use a VPN
VPNs are available for just about any device or platform out there. That said, check out the following guides produced by our team on how to set up a VPN on any device:
- Windows
- macOS
- Linux
- Android
- iOS
- Routers (Netgear, D-Link);
- Chrome & Firefox
- Chrome OS
- Amazon FireStick
- Apple TV
- Kodi
- Raspberry Pi
- Smart TVs
- PlayStation
- Xbox
What Are the Advantages and Disadvantages of a VPN?
There are numerous benefits to using VPNs. So, let's take a brief look at some of the most prominent ones.
- VPNs Unblock Content on the Web: VPNs provide a way to see content that governments don’t want their citizens to see. So if you live in a country that censors the Internet, a good VPN could open your eyes to a world of new opinions. Read our guides on the best VPN for China, UAE, and Turkey - which is where online censorship is at its strongest.
- VPNs Make Public Wi-Fi Safe: You can set up a VPN on any device to ensure that no matter which shady venue’s Web connection you use, it’s as safe as your own home Wi-Fi. So, here's how to use public Wi-Fi safely, and here's the best VPN for public Wi-Fi.
- VPNs Speed Up Your Web Connection: Because of the way VPNs work, your ISP won't see your Web browsing data since it’s all hidden inside your VPN tunnel. That means you get all the speed your connection can provide, minus a little VPN overhead, of course. So, if you ever wondered how to bypass ISP throttling, you’ve just found your answer.
- VPNs Secure Your Mobile Internet: As soon as you leave the comfort of your home Wi-Fi hotspot, you’re probably switching to your mobile data provider. If you don’t have a VPN on your phone, you’ll start leaking private data through your mobile provider the second you’re out of your home Wi-Fi range.
VPNs are beneficial in a huge number of ways - but they also come with some disadvantages. Here's more information about that side of VPN services:
- VPNs Aren't All-In-One Security Solutions: As explained earlier, VPNs won't protect you against malware. They're also not a replacement for dedicated firewall apps. As such, they don't handle every possible aspect of your cyber-security.
- VPNs Can't Unblock Every Single Website: Today's VPNs are hugely powerful in terms of unblocking websites. However, so are the efforts of websites to prevent VPNs. Luckily for you, there's plenty you can do to bypass VPN blocks.
- VPNs Slow Down Unthrottled Connections: If your Internet connection isn't throttled by your ISP, a VPN will slow you down. A capable VPN service will make your connection slower by 10-20%, on average.
Want to take a much deeper look at all the things mentioned just above? If you do, check our guide to the pros and cons of using a VPN.
How Does a VPN Protect You?
A VPN protects you by using its servers to process your data. That means all your incoming and outgoing data is routed through your VPN's servers, going through a process of encryption. So, before your data reached the Internet, it becomes unreadable to anyone else (including your Internet provider).
You might be wondering what's the purpose of encrypting your data. Well, VPNs use encryption and data obfuscation to ensure the privacy of your sensitive and personal information. That puts an end to data tracking, data logging, ISP snooping, and more. In simpler terms, VPNs use fully automated systems to ensure your privacy on the Internet.
Check our guide explaining what does a VPN protect you from, if you're willing to take a deeper dive into this topic.
Can a VPN Be Tracked?
In general, yes - a VPN can be tracked. However, that doesn't happen in the way you might expect. Tracking a VPN doesn't have to mean that your personal data is exposed.
In other words, it's difficult to hide the fact that you use a VPN. Since encryption is involved, your Internet provider will know that you use a VPN. However, it won't know what you do online. So, even though your Internet provider can track your VPN, it can't track the contents of your data tunnel (you remain more than safe).
Here's what does your ISP see when you use a VPN (here's a hint - not much). Also, check our guide that explains whether a VPN can be tracked and blocked by your ISP.
Can a VPN Be Hacked?
In theory - yes, a VPN can be hacked. However, it's close to impossible to hack a VPN in practice. That's because VPNs (especially premium ones) employ expansive systems of data protection measures. Even if someone gets to their servers, accessing user information would not be possible if no-logs policies are active.
When it comes to your locally installed VPN app, the situation is also positive. As explained in our guide on how to hack a VPN, a malicious actor would need to identify and exploit a Wi-Fi vulnerability to access your device. Unless you're a high-risk target, it's hard to imagine something like that happening.
In fact, VPNs protect you from hacking attempts. More precisely, they're highly effective in protecting you against malicious online ads, malicious browser takeovers, clickjacking, IoT attacks, DDoS attacks, as well as MITM (man in the middle) attacks.
Learn more in our guide that explains whether a VPN can be hacked.
Can a VPN Track My Online Activity?
In theory, yes - a VPN can track your online activity as you use its VPN servers to reroute your Web traffic. However, not every VPN will track what you do online.
That's precisely why you need to be careful when choosing a VPN. Our strong recommendation is to pick a VPN with a proven and verified no-logs policy. Those VPNs have been audited to test their claims, and they'll have zero knowledge of your online activities.
Most reputable VPNs go through regular audits to prove their no-logs claims. That said, you can learn more about ExpressVPN's audit, NordVPN's audit, TunnelBear's audit, ProtonVPN's audit, VyprVPN's audit. To discover more, check out the best no-logs VPN.
Can My ISP See That I Am Using a VPN?
Yes, your ISP will see you using a VPN. However, it won't see the contents of your VPN tunnel, which means that your privacy will be kept safe in the most secure way possible.
As mentioned in this article, your Web traffic won't simply vanish once you start to use a VPN. However, it will be placed into a secure and encrypted VPN tunnel, making your data scrambled and out of anyone's reach. That's why your ISP will see that you use a VPN - but it won't see what you do online, which is how you can hide your Web browsing history.
How Do VPNs Affect My IP Address?
VPNs change your IP address, typically assigned to your device by your ISP (Internet service provider). That's one of the ways VPNs protect your privacy.
It's often said that VPNs hide your IP address, which stands true. However, know that your IP won't simply vanish. Instead, your VPN will replace it with its own IP, which can point to a different country if you decide to use a VPN server in a different country.
That's precisely how you can unblock websites, as they won't know your true location.
Can I Create My Own VPN?
Yes, you can create your own VPN if you're willing to dive into a DIY project, which can be an option for more advanced VPN users. However, it's important to know that creating your own VPN can be more expensive in the long run than getting a commercial VPN subscription.
There are several ways to create your own VPN, like using a VPN-compatible router or turning your old computer into a server. You'll find all the information you need from our guide to set up your own VPN server at home.
Can I Use a VPN for Torrenting?
Yes, you can use a VPN for torrenting. In fact, a P2P VPN is your best shot at downloading torrent files anonymously - without being afraid of receiving a copyright infringement notice.
If you know how torrents work, you already know the importance of protecting what you do online. Even if you stick to legal torrent websites only, ISPs will throttle your Web connection, preventing you from downloading torrents. As you can already imagine, this is where the best VPN for torrenting comes into play.
As noted in our ultimate guide to downloading torrents, P2P traffic uses a network of computers to create a chain of command. Therefore, as long as you're in that network, your information (like your IP address and your location) becomes visible to other participants of that network.
By using a VPN, you can hide that information from other P2P users and your ISP. So, make sure to have a VPN the next time you use any of the popular torrent clients or any of the worldwide-used torrent websites.
Can I Use a VPN for Media Streaming?
Yes, you can use a VPN for media streaming - especially if you want to unblock new types of media platforms that might not be available in your country.
If you want to stream media using a VPN, we highly recommend checking our guide to the best VPN for streaming. However, it's also a good idea to check different VPNs based on your favorite streaming platforms.
With this said, here's how you can watch Netflix, Hulu, Hulu + Live TV, Paramount Plus, Discovery Plus, Disney Plus, YouTube TV, Amazon Prime Video, and HBO Max outside the US.
Will a VPN Slow Down My Web Connection?
Yes, a VPN will slow down your Web connection because, when using a VPN, your data travels through an additional server. This means it has a longer route, which is one of the reasons why you might experience some throttling.
Different VPNs impact your Web connection in different ways, so make sure to do your research before buying a subscription. With that said, here's how much a VPN can slow down your Internet speed. And in case you've been wondering if a VPN consumes more data than normal, keep in mind that you won't even notice that overhead.
To help you find the best VPN, we have our own guide to the fastest VPN services. But also, remember that there's plenty you can do to speed up slow VPNs, which also depends on the type of VPN protocol you plan on using.
How Much Do VPNs Cost?
Most VPNs come with several subscription plans, allowing you to pay on a monthly or yearly basis. This way, VPNs can cost from around $10.00 to around $15.00 per month. However, paying upfront usually brings you steep discounts of more than 50%.
That means that if you break down their yearly prices into monthly payments, you'll need to pay from around $2.50 to around $8.00 (check out the best cheap VPN options). Of course, by choosing a yearly plan, you need to pay for the whole year upfront.
It's also worth mentioning that you can find some pretty great deals from time to time. We have our article on the best VPN deals, which we frequently update, so make sure to take a look.
Can I Try VPNs Free of Charge?
Yes, you can try some VPNs for free, but not many VPNs offer trials. That's because it would be easy for individuals to use different email addresses and take advantage of those trials. However, here is a list of free trial VPN services that don't charge you.
Please note that the majority of VPN trials will need your personal information. So, if you aren't comfortable providing such data, here are the best completely free VPN trials (no credit card required),
Are There Completely Free VPN Services?
Yes, there are some free VPN services that won't charge you a single dollar. However, since you're not paying for those, you become the product.
As shown by numerous reports before, free VPNs leak your personal data. They also collect your personal data and sell it to advertisers. And on top of that, they can't bring the same level of security as commercial VPNs do.
So, can you find free VPNs out there? Yes, and you don't even have to look too hard. Should you use those free VPNs? Definitely no, since free VPNs aren't safe, and they can easily become a gateway to malware, adware, and more.
What Are VPN Routers and Should You Use One?
The best way to secure multiple devices at once is to buy a VPN router. By running a VPN that way, every device connected to that router gets the protection provided by your VPN service.
We'll be honest with you, and we'll say that installing a VPN on a router might be a bit technical for inexperienced users. However, there are many helpful guides online, including ours. With that said, make sure to check out how to choose a VPN router before buying one.
In addition to using VPN routers, you can also use DD-WRT routers. As their name says, these are powered by open-source DD-WRT firmware, which is easy to use and comes with plenty of fine-tuning.
The best thing is - there are plenty of different options out there. We have our guides for the best DD-WRT routers under $50 as well as routers under $100, in addition to the best DD-WRT routers overall.
How Do I Troubleshoot a VPN?
The best way to troubleshoot a VPN is by connecting to a different VPN server, switching to another VPN protocol, as well as by reinstalling/updating your VPN software.
You'll be happy to know that resolving VPN issues is typically easy. We gave you 20+ actionable tips in our central VPN troubleshooting guide, which should be your go-to resource in case of any troubles. We also have a guide explaining why your VPN doesn't work, as well as a guide to VPN error code fixes (useful if your VPN is showing you a specific code).
Finally, once you resolve your issues, you'll want to make sure to know how to check if your VPN works properly. Ensure the integrity of your VPN tunnel is intact, which means your private data won't leak on the Web. Then, continue using the Web without any fear.
Is a VPN Worth It?
Yes, definitely - VPNs are worth it! As explained throughout this guide, getting a VPN means you'll be taking care of your digital privacy, which has become imperative in this day and age.
However, keep in mind that now all VPNs are worth it. In fact, it's better not to use a VPN that to use a free or an unknown one. Since they handle your data, they can also take advantage of your data. So, make sure to pick a trustworthy one, with a long history of serving its users.
We'll also note that most of today's VPNs come from several companies, as the global VPN market is currently going through consolidation. So, here's which companies own today's most popular VPN services, which should be an important aspect of choosing a VPN.
Final Thoughts
As long as you pick a trustworthy and reputable VPN, you can rest assured that your privacy is protected on the Web. So, no matter if you want to keep trackers at bay, unblock sites, download torrents, or play online games - getting a VPN is the best choice you can make right now.
Just keep in mind that it's imperative to go for a reputable VPN brand. Trying to save money by picking a free VPN or an unknown one can actually harm your privacy. So, if you decide to use a VPN, remember that spending a few dollars more per month can actually go a very long way.
We hope that you liked our comprehensive guide trying to answer the question of - what is a VPN? If you have any questions for us, make sure to post them just below. Thanks for reading!